
Managed Security Services
For Proactive I.T. Security
Proactive Blocking and Threat Hunting For Emerging Threats And Instant Active Remediation Response When A Threat Is Identified.
Our Managed Service Service Packages
Holistic IT Services to Design, Build and Manage to Achieve
Business Outcomes At A Predictable Per User Cost
Vigilance
Essential Security
Perfect for companies needing a fractional
security solution that partners with company internal IT staff, but without the expensive tooling and certified staffing requirements.
• 24/7/365 Security Operations Center (SOC) with active human monitoring
• Incident escalation upon detection to your
internal team for containment and mitigation
•Threat intelligence that exposes the
cyberattacker and their online infrastructure
Vigilance
Professional Security
Ideal for the larger enterprise customers and entities with regulatory and policy requirements.
• Vigilance Essential +
• Real Time Active Response and Incident
Management
• Threat hunting that seeks out threats before they land to prevent exploitation (and frustrate hackers).
• Weekly meeting availability
• Monthly SOC Reports
Vigilance
Ultimate Security
Our expanded service offering allows you to free up your team to focus on what they do best.
• Vigilance Professional +
• M365 Support and license management
• Vulnerability Management to monitor and
proactively fix known vulnerabilities found
within your network.
Managed Firewall
Our managed firewall service takes the
headache and worry from making sure your
ACL’s and policies match organizational
outcomes and goals.
This service includes firmware upgrades and vulnerability patching.
| 24/7/365 Active Monitoring | Incident Escalation | Threat Intelligence | Incident Containment | Active Response | Threat Hunting | M365 Support | Vuln Management via USM | |
| Essential | √ | √ | √ | + | + | + | ||
| Professional | √ | √ | √ | √ | √ | |||
| Ultimate | √ | √ | √ | √ | √ | √ | √ | √ |
Security Incident Workflow
We utilize the NIST Cyber Security Framework to Integrate assets into a common logging and alerting platform and monitor, analyze and investigate IT threats.
Integration
Integration of cloud and on-premise SIEM tools with security endpoints.
Collection
Collection of cloud and on-premise user data, device, application and infrastructure log data.
Detection & Reporting
Detection and Reporting of prioritized threats with processes to root out false positives.
Investigation
Investigation of threats in real time to determine size and nature of the threat.
Containment & Eradication
Containment of the endpoint and/or identity to prevent further spread and eradication of all known vectors with strategic remediation to prevent follow up incidents.
Review
Review includes post-incident reports, lessons learned, root cause analysis and policy considerations.
Why TorchLight?
At TorchLight, our “why” is simple: we exist to serve our customers and protect them from the relentless threat of hackers. This mission drives everything we do, setting us apart in the Secured and Managed IT landscape.
We foster a culture of candor, transparency, service, proactive communication and a growth mindset, all aimed at supporting our clients’ needs. We seek trusted partnerships with organizations that share our values, prioritizing open dialogue and a win/win mindset.
Together, we ensure that IT security goals are not only met but exceeded, safeguarding business continuity every day. Our people are our greatest asset, unified by our mission to secure and serve our customers and frustrate the hackers.
The Way Forward – TorchLight Blog
-
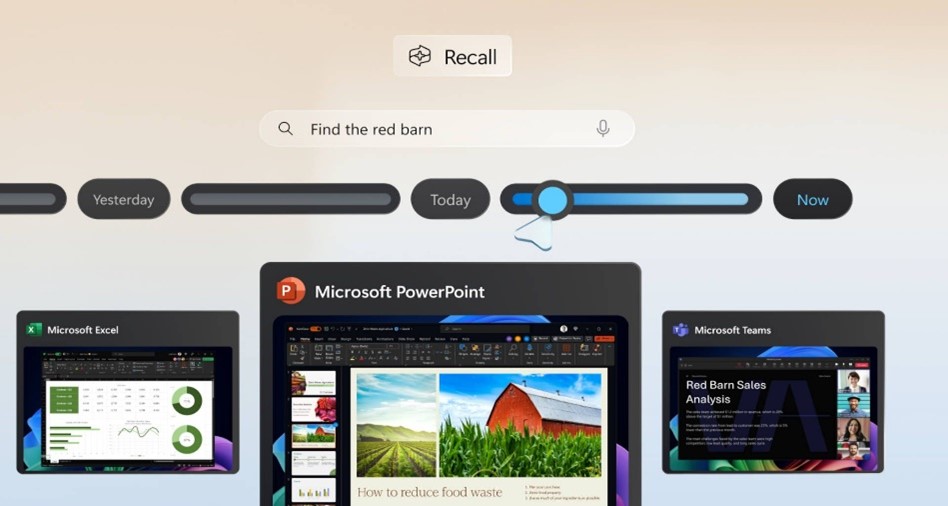
Windows Recall: What You Need to Know — And Why It Matters
Microsoft’s upcoming Recall feature for Windows 11 Copilot+ PCs is shaping up to be one of the most talked-about developments in workplace technology this year. Designed to boost productivity by taking periodic snapshots of user activity for easy, searchable recall, the feature promises convenience — but also raises serious privacy and security concerns.
-

Strengthening Your Security Posture with EDR & ITDR
Cyber attackers aren’t just targeting networks anymore—they’re going after identities and endpoints at scale. In fact, over 80% of breaches involve compromised credentials or exploited devices. In this month’s service spotlight, we break down two critical layers of modern cyber defense—Endpoint Detection and Response (EDR) and Identity Threat Detection and Response (ITDR)—and show how they…
-

Washington State Expands Sales Tax to IT Services
A new Washington State law—Senate Bill 5814—goes into effect on October 1, 2025, and it will significantly impact customers located in Washington who receive IT, digital, and tech-related services. This change will apply regardless of where the service provider is located, and may affect how your organization is billed by vendors like MSSPs, cloud providers,…