Managed IT Services And Cybersecurity For Family Offices
Discreet, defense-in-depth IT for multi-generational wealth – built on trust, privacy, security, and stability
Why TorchLight for Family Offices?
We prioritize trust and privacy above all. Our background-checked, US-based team operates with minimal visibility, proactive communication, and a security-first mindset. The outcome is stability – technology that quietly protects your people and assets while you focus on stewardship.
Growth Focused IT for Family Office Investments
Friendly service desk support, endpoint security, patching, backups, and cloud productivity are the basics. We implement them consistently so your business stays secure and operational, without slowing your team down.
Endpoint Detection and Response
Lightweight protection that monitors in real time, quarantines threats, and auto-remediates – without interrupting your day.
Vulnerability Management and Patching
Automated OS and app updates happen after hours to reduce disruption and close security gaps quickly.
Reliance Backups
Disaster-recovery-ready backups for workstations, servers, and cloud data – including M365 email and SharePoint.
Microsoft 365 Support
Simplified administration for email, identities, SharePoint, and Azure AD – managed in one pane of glass by our team.
24x7x365 Security Monitoring
We watch your business 24×7 and protect you in real time from threat actors.
Identity Threat Detection and Response (ITDR)
ITDR protects your business by monitoring and responding to suspicious account activity to keep user identities and data secure.
Confidentiality & Governance – How We Protect Your World
• Discretion by design: background-checked, US-based engineers; role-based access, least privilege, and strict need-to-know controls.
• Secure collaboration: hardened M365 tenants, identity governance (MFA/SSO/conditional access), secure file sharing.
• Privileged Access Management: vaulting, approvals, and auditable session controls for high-risk accounts.
• Vendor & risk oversight: vendor assessments, documentation, and executive-ready reporting.
• VIP protection: secure travel playbooks, executive device hardening, and rapid response.
• Continuity & recovery: Reliance Backups for endpoints, servers, and cloud data; tested recovery plans.
• Network & endpoint protection: managed AV/EDR, patch automation, and 24/7 monitoring.
• Incident readiness: named response team, real-time containment, forensics coordination.
• Communication security: encrypted email, secure messaging options, and mobile device management.
• Board-level visibility: QBRs with health scorecards, risk register updates, and clear next actions.
Latest Insights & Blog
Expert insights on cybersecurity, compliance, and IT strategy.
-
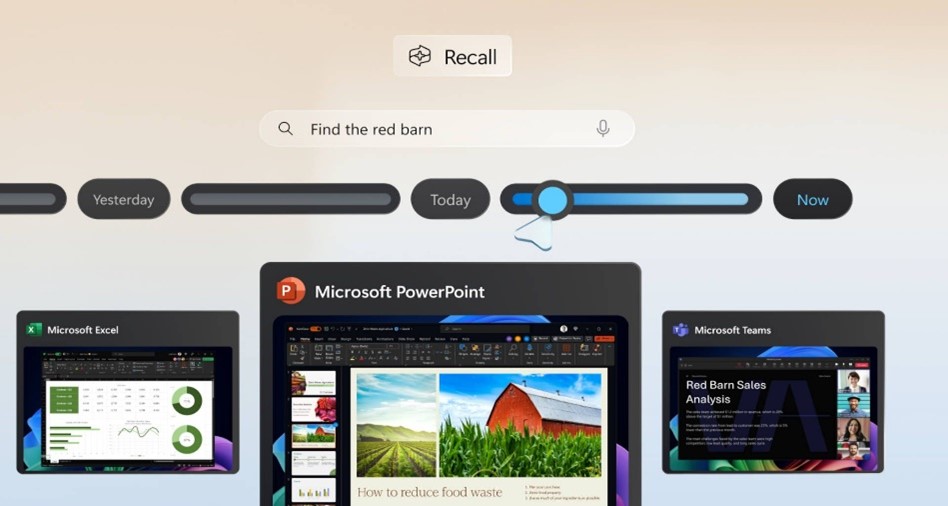
Windows Recall: What You Need to Know – And Why It Matters
Microsoft’s upcoming Recall feature for Windows 11 Copilot+ PCs is shaping up to be one of the most talked-about developments in workplace technology this year. Designed to boost productivity by taking periodic snapshots of user activity for easy, searchable recall, the feature promises convenience – but also raises serious privacy and security concerns.
-

Strengthening Your Security Posture with EDR & ITDR
Cyber attackers aren’t just targeting networks anymore – they’re going after identities and endpoints at scale. In fact, over 80% of breaches involve compromised credentials or exploited devices. In this month’s service spotlight, we break down two critical layers of modern cyber defense – Endpoint Detection and Response (EDR) and Identity Threat Detection and Response…
-

Washington State Expands Sales Tax to IT Services
A new Washington State law – Senate Bill 5814 – goes into effect on October 1, 2025, and it will significantly impact customers located in Washington who receive IT, digital, and tech-related services. This change will apply regardless of where the service provider is located, and may affect how your organization is billed by vendors…
-
The Windows 10 to Windows 11 Transition
Another large milestone looms in the Microsoft ecosystem as Windows 10 is (mostly) officially sunsetted on October 14, 2025. Meaning, no new security updates will be produced by Microsoft, unless you purchase an ESU/Extended Security Update license for up to three years that will allow Windows 10 to continue receiving security updates on a regular…
-
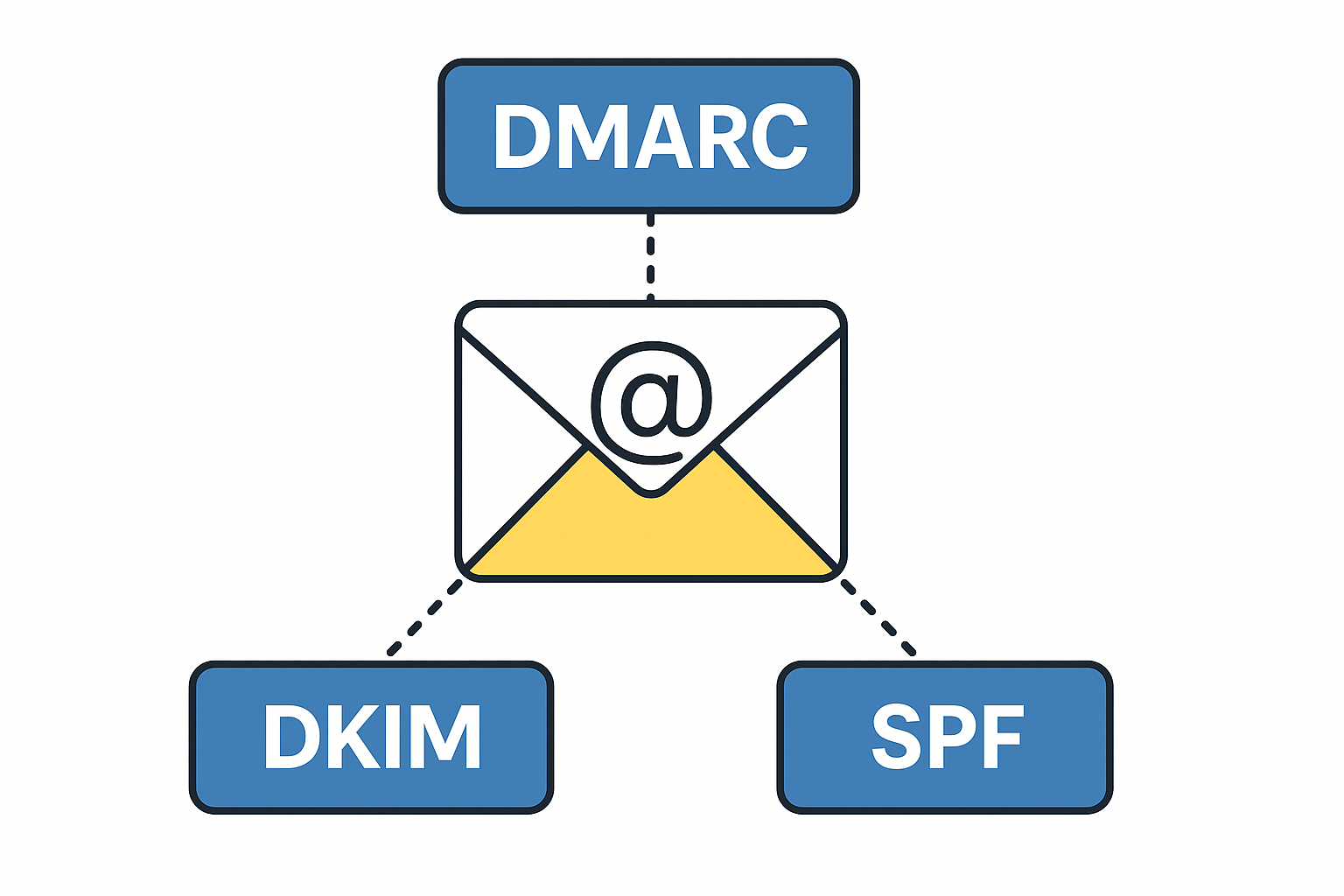
Tech Talk – What is DMARC, DKIM, SPF & Why Do I Want To Know?
DMARC, DKIM and SPF are three separate email authentication protocols that build layers of security around email delivery and integrity. Used in conjunction with each other, they provide a durable layer of protection for inbound emails and brand protection to prevent bad actors from sending emails using your business domain name. These tools provide domain…
-
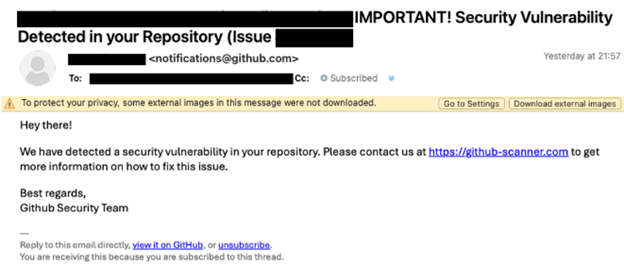
Beware of the ClickFix Scam!
TorchLight’s Threat Intelligence team has uncovered a resurgence of a phishing scam called ‘ClickFix,’ initially identified in late 2024 but now widely used by cybercriminals in 2025.
-

Microsoft Teams Phishing Attacks
TorchLight Security Operations Center continues to hear about Microsoft Teams as the vector to social engineering, phishing and spearphishing attempts by hackers. Given the volume of noise, we thought we’d publish what we know and how to defend against these attacks.
-

New Mac Vulnerability – Banshee MacOS Stealer
Our security operations center was notified of a new and novel bug that can affect all Macs. Titled “Banshee MacOS Stealer”, this first came on the scene in mid-2024 as a “malware as a service” exploit.
-

NIST Cybersecurity Framework 2.0 – Considerations for Small to Medium Sized Businesses
The NIST Cybersecurity Framework is a methodology designed to simplify the process of planning, implementing, managing and responding to threats from a holistic point of view in the Information Technology Delivery and Security space. It is specifically designed for organizations that either have no or very little cybersecurity planning, processes or responses to emerging threats.
-

Industry Impact of Ransomware Attacks
Find out why academic institutions, automobile dealerships, and the utility sector are all high-profile targets of ransomware attacks.
