HIPAA-Ready Cybersecurity For Healthcare Organizations
Clinic-quiet IT, PHI protection, and predictable cost – for providers, labs, biotech, and research teams
What keeps healthcare & life sciences leaders up at night
- HIPAA/HITECH compliance gaps and audit readiness
- EHR downtime impacting patient care and revenue
- Ransomware, BEC, and medical device exposure
- Research data integrity, access control, and chain-of-custody
- Vendor sprawl across EHR, imaging, labs, and specialty apps
Outcomes TorchLight delivers
- Compliance-ready policies, risk assessments, and evidence
- Uptime targets aligned to clinic hours and maintenance windows
- Segmented networks and managed EDR to reduce attack surface
- Protected research workflows with access, logging, and backups
- Vendor coordination and single-point accountability
Why TorchLight for Healthcare & Life Sciences?
Because you need a partner that understands clinical and research workflows, coordinates vendors without drama, and reports to leadership and compliance with clarity. We deliver trust, security, and stability – so your team can deliver care and accelerate discovery.
Secure, Stable IT for Healthcare
Friendly service desk support, endpoint security, patching, backups, and cloud productivity are the basics. We implement them consistently so your business stays secure and operational, without slowing your team down.
Endpoint Detection and Response
Lightweight protection that monitors in real time, quarantines threats, and auto-remediates – without interrupting your day.
Vulnerability Management and Patching
Automated OS and app updates happen after hours to reduce disruption and close security gaps quickly.
Reliance Backups
Disaster-recovery-ready backups for workstations, servers, and cloud data – including M365 email and SharePoint.
Microsoft 365 Support
Simplified administration for email, identities, SharePoint, and Azure AD – managed in one pane of glass by our team.
24x7x365 Security Monitoring
We watch your business 24×7 and protect you in real time from threat actors.
Identity Threat Detection and Response (ITDR)
ITDR protects your business by monitoring and responding to suspicious account activity to keep user identities and data secure.
Compliance & Resilience – What’s Included
Compliance readiness: policies, BAAs, risk assessments, and evidence aligned to HIPAA/HITECH, 21 CFR Part 11, and common frameworks.
Operational resilience: maintenance windows aligned to clinic hours; change management and test plans for EHR and imaging.
Vendor oversight: coordinated escalation with EHR, imaging, lab, and specialty vendors; due-diligence evidence for committees.
Cyber-insurance support: control implementation plans and attestations to stabilize renewals.
Leadership visibility: QBRs and scorecards translating IT risk to business impact and next actions.
Identity & access controls: MFA, SSO, conditional access, least privilege, and privileged account vaulting with approvals and logging.
Endpoint & server protection: managed AV/EDR, patching, and configuration baselines with 24/7 response.
Backups & recovery: Reliance Backups for endpoints, servers, and M365 with tested restores and reporting.
Secure collaboration: hardened M365 tenants, secure file sharing, and mobile device management.
Incident response: named handlers, rapid containment, forensic coordination, and post-incident reporting.
Latest Insights & Blog
Expert insights on cybersecurity, compliance, and IT strategy.
-

Why Device Logins Just Became a Liability
A new phishing technique has compromised more than 340 Microsoft 365 organizations since February 2026, and not one of them lost a password. Here is what credit unions, healthcare practices, and RIA firms need to ask their IT team this week, before an examiner does.
-

How Credit Unions Can Stay Audit-Ready Using Outsourced IT Managed Services
How Credit Unions Can Stay Audit-Ready Using Outsourced IT Managed Services Every credit union leader knows the feeling: an NCUA exam is approaching, and the scramble begins, pulling together logs, chasing down documentation, trying to prove that controls are actually in place. It’s stressful, expensive, and entirely avoidable. The root problem is almost always the…
-
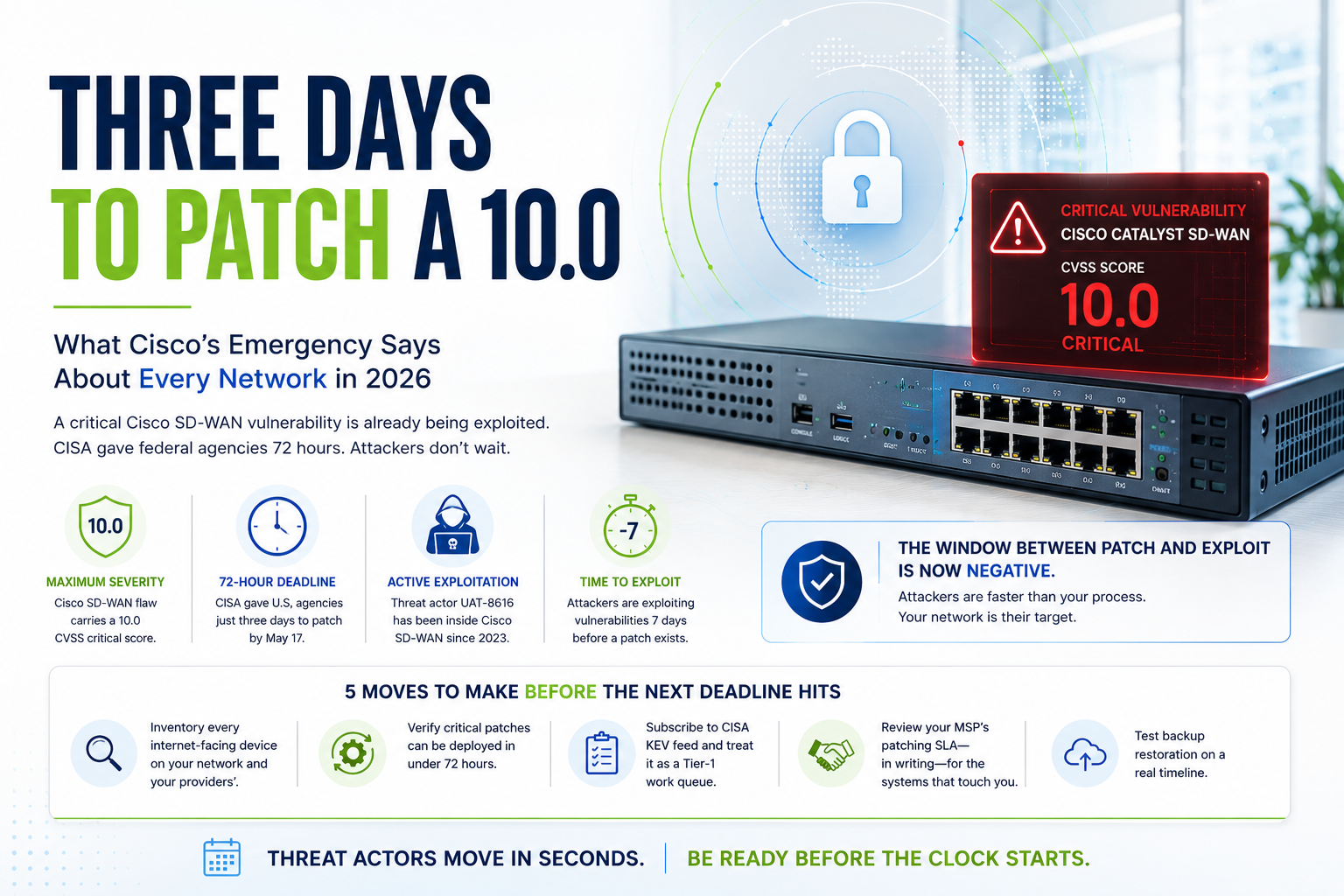
Three Days to Patch a 10.0: What The Cisco SD-WAN Vulnerability Says About Every Network in 2026
Two critical ScreenConnect vulnerabilities, including a CVSS 9.0 flaw under active exploitation by nation-state actors, have opened a direct tunnel into the networks of banks, RIAs, and healthcare practices. The federal patch deadline is May 12, 2026. Here’s what to check, what to hunt for, and how to close the door before examiners or attackers…
-
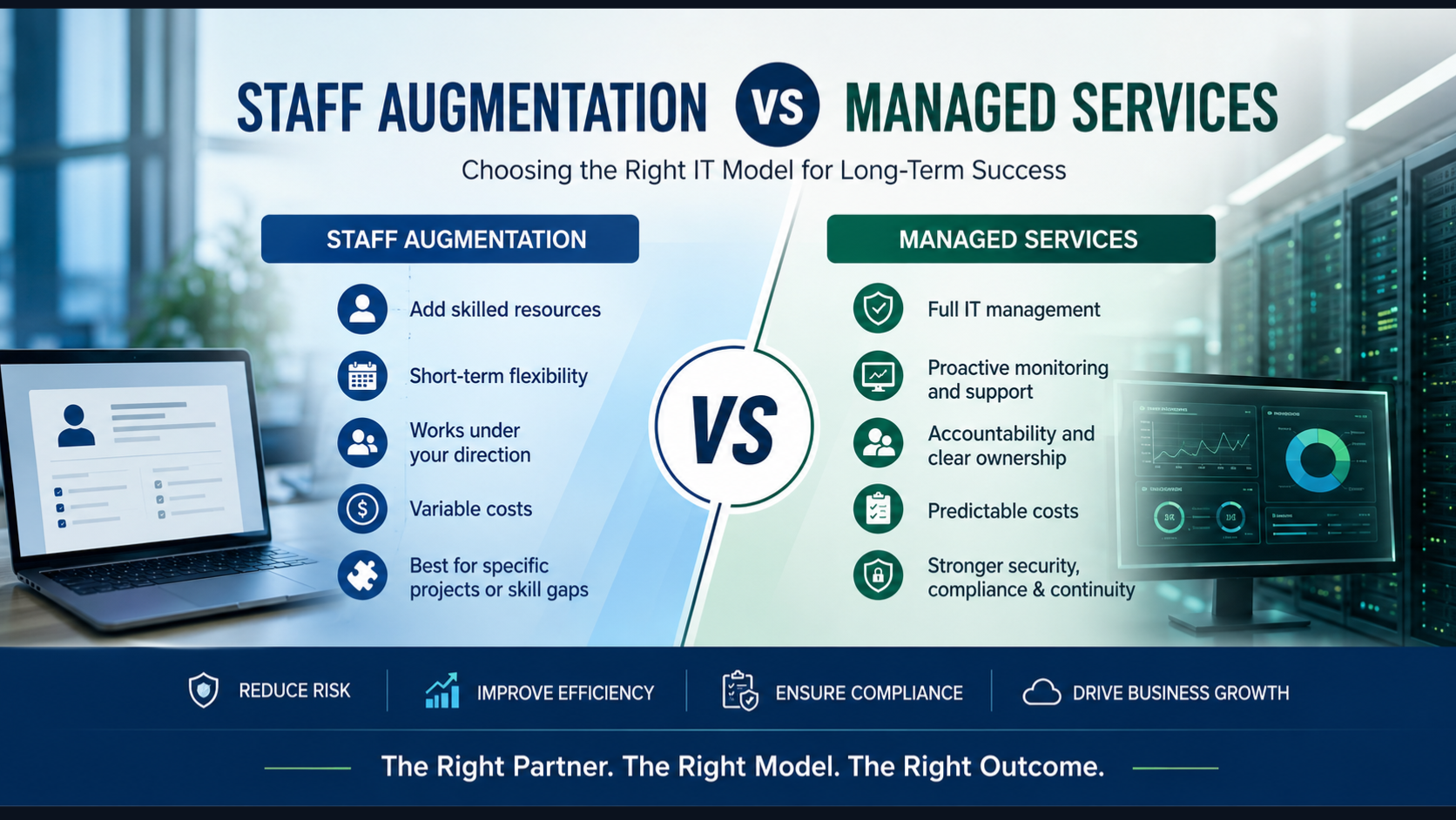
Staff Augmentation vs Managed Services: What IT Leaders Need to Know Before Choosing
Not long ago, the answer to an IT gap was simple: hire a contractor, bring in a temp resource, or extend a vendor engagement. Staff augmentation felt flexible, affordable, and fast. For many organizations, it still has a role to play. But the IT environment has changed dramatically. Ransomware attacks are targeting mid-market companies and…
-

Your Remote Access Tool Could Be Your Biggest Threat
Two critical ScreenConnect vulnerabilities, including a CVSS 9.0 flaw under active exploitation by nation-state actors, have opened a direct tunnel into the networks of banks, RIAs, and healthcare practices. The federal patch deadline is May 12, 2026. Here’s what to check, what to hunt for, and how to close the door before examiners or attackers…
-

Managed IT Services Pricing in 2026: A Complete Guide for Businesses
When businesses start researching managed IT services, one question usually comes first: “How much should managed IT actually cost?” And honestly, the answers online can feel confusing. One provider may quote a few hundred dollars per month, while another charges thousands for seemingly similar services. Some include cybersecurity, backups, and cloud management in their pricing,…
-
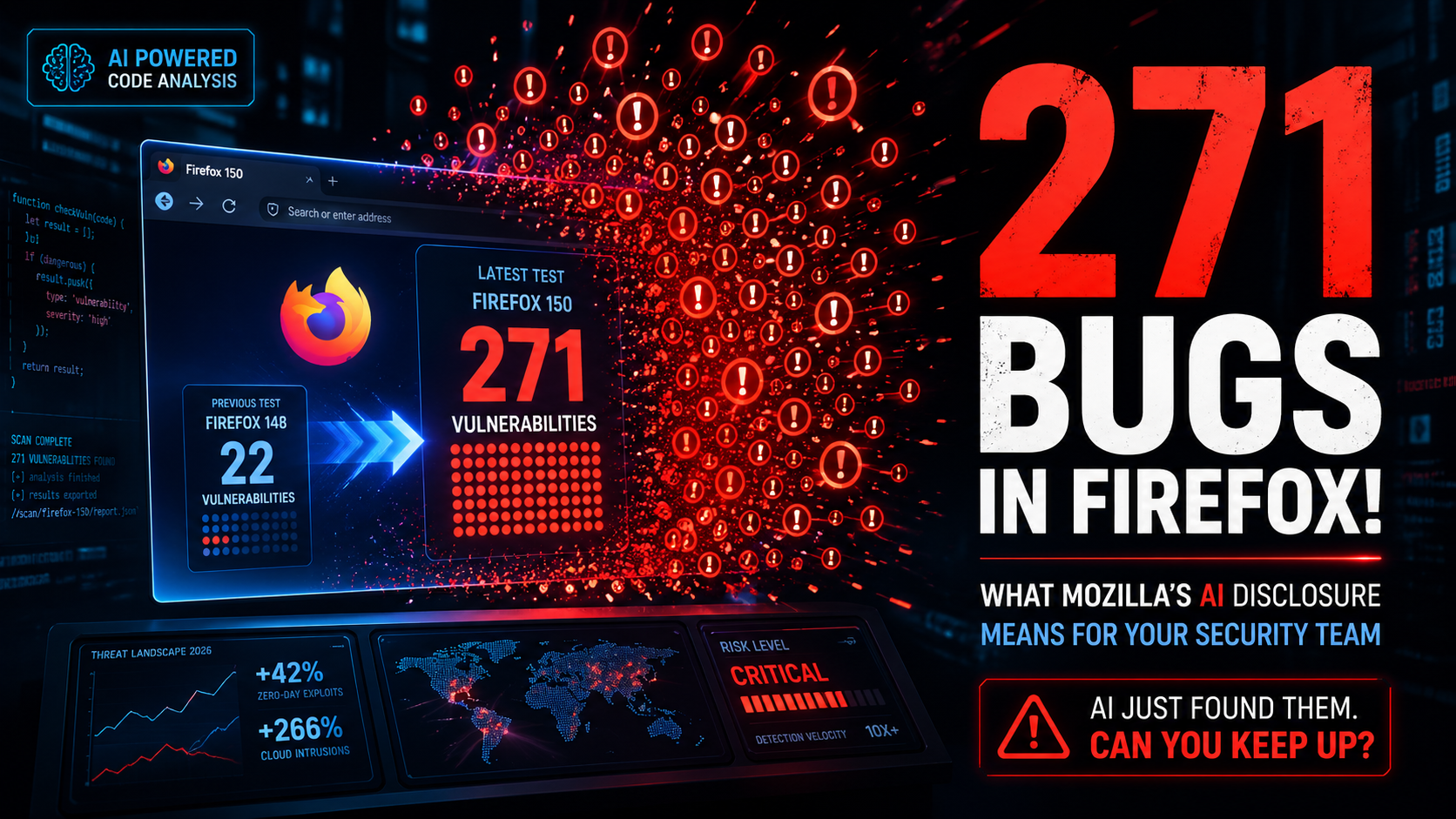
271 Bugs in Firefox! What Mozilla’s AI Disclosure Means for Your Security Team
Surfacing 22 new bugs in Firefox 148 was already an outlier. Surfacing 271 in Firefox 150 was something else entirely.
-

AI Phishing Attacks in 2026: Why Regulated Organizations Are at Risk
Phishing volume and sophistication have surged in 2026, driven by generative AI that lets attackers produce flawless, personalized lures at scale. Traditional email filters and “spot the typo” training can’t keep up.
-

Why Regulated Businesses Need Managed Security Services (MSSP) in 2026?
Executive Summary Managed Security Services Providers (MSSPs) deliver 24/7 threat monitoring, detection, and response capabilities that most organizations can’t build cost-effectively in-house. For regulated industries—credit unions, healthcare providers, government agencies, and wealth management firms—MSSPs have evolved from optional vendors to strategic necessities. This comprehensive guide explains what MSSPs actually do, who needs them, how to…
-
AV vs EDR vs MDR vs ITDR: What Regulated Organizations Actually Need in 2026
The Cybersecurity Tool Problem No One Talks About Here’s a conversation that happens more often than it should in boardrooms across financial services, healthcare, and government sectors: “Do we have antivirus?” the executive asks. “Yes,” the IT manager confirms. “Then we’re protected, right?” “…Sort of.” That “sort of” is where data breaches live. That hesitation…
