AI Workflow Automation And Business Process Automation Services
Design, document, and automate the work that runs your business so it flows the same way, every time.
AI & Workflow Automation Services
From scattered tasks and manual rework to documented, automated workflows that support growth and compliance.
We work with platforms such as Microsoft Copilot, Power Automate, n8n and other automation tools, but we remain tool agnostic so the AI automation services we provide fit your systems, controls, and people.
What AI & Automation Change For Your Team
We help you move beyond one-off bots and scripts into intelligent automation solutions – reliable systems that free up capacity, improve accuracy, and make your operating model more predictable.
Process Discovery and Design
We map your current workflows, identify bottlenecks, and design a future state that reduces handoffs, errors, and rework while aligning with your controls.
Workflow Automation Integration Services
We connect the tools you already own so data moves cleanly between systems and the right people are notified at the right time.
Copilot and M365 Enablement
We help your team get real value from Microsoft Copilot and related tools by aligning prompts, governance, and digital workflow automation with your daily work.
Human-in-the-Loop Guardrails
We design approvals, reviews, and controls into your AI driven business automation so AI speeds up work without creating new risk.
Monitoring, Metrics, and Improvement
Dashboards and simple metrics show where AI process automation services save time and where the process still needs tuning — so you keep improving over time.
Compliance and Risk Aligned Automation
For regulated industries we align automations with exam expectations, documentation needs, and your cyber and data governance requirements.
Why TorchLight for AI Workflow Consulting Services?
At TorchLight, we believe AI workflow automation should make your business more predictable, not more chaotic. We focus on the systems that run your organization, then apply automation where it reduces noise and risk instead of creating new problems.
Our team blends IT, security, and AI business process automation expertise so your automations respect role-based access, audit requirements, and examiner expectations. We prioritize open communication and a partnership mindset so leaders stay in control of outcomes while we handle the technical details.
The result is a clear process automation strategy consulting roadmap, documented workflows, and automations that support your people. You gain capacity, consistency, and confidence that critical processes will run even when key staff are out of office.
Frequently Asked Questions
How does TorchLight help with AI Workflow Automation?
AI workflow automation covers the full journey from mapping your current processes to designing, building, and running automated systems that replace manual, error-prone steps. TorchLight helps with process discovery, tool selection, integration, guardrails, and ongoing improvement – so the result is a reliable operating model, not just a one-off script.
What platforms do you use for workflow automation services?
We work with Microsoft Copilot, Power Automate, n8n, and other leading platforms. Our approach to workflow automation services is tool-agnostic. We recommend the platform that fits your existing systems, security controls, and compliance requirements, not the one that’s easiest for us.
How do business process automation services work for regulated industries?
For regulated industries business process automation services require more than just connecting tools. We align every automation with your exam expectations, documentation standards, and data governance requirements – so the efficiency gains don’t create new compliance gaps.
Do you offer AI automation consulting before we commit to a full build?
Yes. We offer an Automation Assessment as a starting point. Our AI automation consulting engagement covers your current workflows, the biggest automation opportunities, the right tools for your environment, and a realistic roadmap – before any build work begins.
What is the difference between enterprise workflow automation and standard automation?
Enterprise workflow automation goes beyond simple task automation. It covers cross-department processes, multi-system integrations, compliance controls, role-based access, and governance – the kind of structure that regulated organizations and larger businesses need to scale automation safely.
How do you handle AI governance and human oversight in AI business automation solutions?
Every set of AI business automation solutions we build includes human-in-the-loop guardrails – approval steps, review checkpoints, and escalation paths that keep your team in control of outcomes. AI speeds up the work; your people remain accountable for the decisions.
What does intelligent workflow automation look like in practice?
Intelligent workflow automation means your systems don’t just move data — they make context-aware decisions. For example: routing an approval based on dollar threshold, flagging an anomaly for human review, or triggering a compliance documentation step automatically when a process milestone is reached.
Is TorchLight an AI automation services provider or a traditional IT firm?
Both. As an AI automation services provider with deep roots in IT and cybersecurity, TorchLight brings something most pure automation firms can’t: the ability to design automations that respect your security controls, compliance requirements, and IT infrastructure from day one.
Can you help with enterprise AI automation consulting for multi-department rollouts?
Yes. Our enterprise AI automation consulting engagements are designed for organizations rolling out automation across multiple teams or departments. We work with leadership, IT, and operations together to ensure the rollout is structured, documented, and aligned with your overall governance framework.
What are enterprise workflow automation services, and does TorchLight offer them?
Yes. Our enterprise workflow automation services cover end-to-end automation design, integration across business-critical systems, compliance alignment, and ongoing monitoring — built for organizations with complex environments, regulated processes, or multi-location operations.
Latest Insights & Blog
Expert insights on cybersecurity, compliance, and IT strategy.
-

Why Small Businesses Are the New Cyber Targets – And How to Stay Protected
Cybercriminals target the vulnerable, not just the big guys. For small businesses in regulated industries, the risks are real – compliance gaps, lost trust, even financial collapse. At TorchLight, we make enterprise-grade cybersecurity practical and personal, with strategy-led protection built for your business.
-
Windows Recall: What You Need to Know – And Why It Matters
Microsoft’s upcoming Recall feature for Windows 11 Copilot+ PCs is shaping up to be one of the most talked-about developments in workplace technology this year. Designed to boost productivity by taking periodic snapshots of user activity for easy, searchable recall, the feature promises convenience – but also raises serious privacy and security concerns.
-

Strengthening Your Security Posture with EDR & ITDR
Cyber attackers aren’t just targeting networks anymore – they’re going after identities and endpoints at scale. In fact, over 80% of breaches involve compromised credentials or exploited devices. In this month’s service spotlight, we break down two critical layers of modern cyber defense – Endpoint Detection and Response (EDR) and Identity Threat Detection and Response…
-

Washington State Expands Sales Tax to IT Services
A new Washington State law – Senate Bill 5814 – goes into effect on October 1, 2025, and it will significantly impact customers located in Washington who receive IT, digital, and tech-related services. This change will apply regardless of where the service provider is located, and may affect how your organization is billed by vendors…
-
The Windows 10 to Windows 11 Transition
Another large milestone looms in the Microsoft ecosystem as Windows 10 is (mostly) officially sunsetted on October 14, 2025. Meaning, no new security updates will be produced by Microsoft, unless you purchase an ESU/Extended Security Update license for up to three years that will allow Windows 10 to continue receiving security updates on a regular…
-
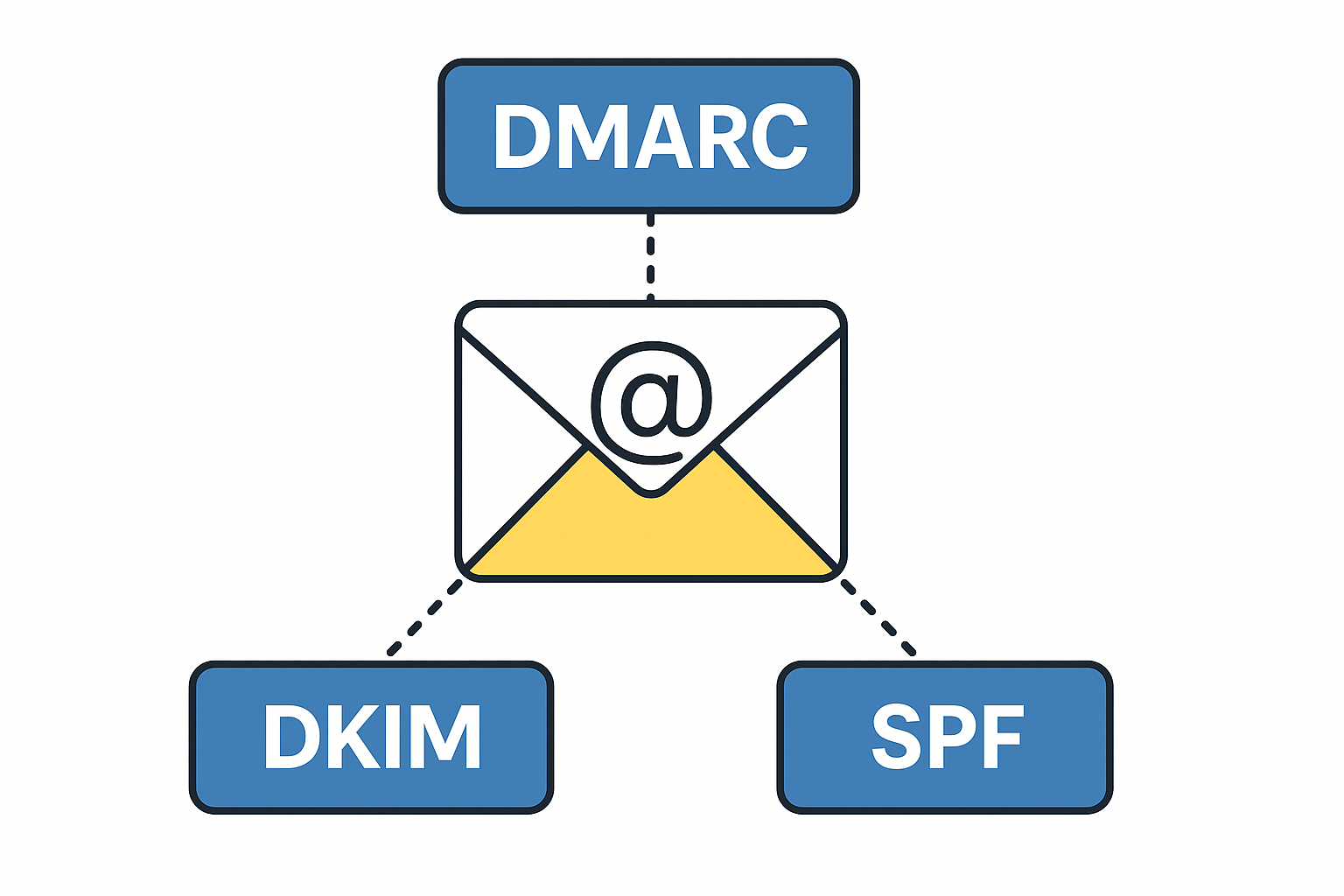
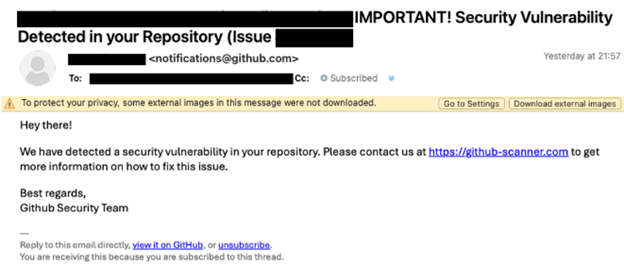
Tech Talk – What is DMARC, DKIM, SPF & Why Do I Want To Know?
DMARC, DKIM and SPF are three separate email authentication protocols that build layers of security around email delivery and integrity. Used in conjunction with each other, they provide a durable layer of protection for inbound emails and brand protection to prevent bad actors from sending emails using your business domain name. These tools provide domain…
-
Beware of the ClickFix Scam!
TorchLight’s Threat Intelligence team has uncovered a resurgence of a phishing scam called ‘ClickFix,’ initially identified in late 2024 but now widely used by cybercriminals in 2025.
-

Microsoft Teams Phishing Attacks
TorchLight Security Operations Center continues to hear about Microsoft Teams as the vector to social engineering, phishing and spearphishing attempts by hackers. Given the volume of noise, we thought we’d publish what we know and how to defend against these attacks.
-

New Mac Vulnerability – Banshee MacOS Stealer
Our security operations center was notified of a new and novel bug that can affect all Macs. Titled “Banshee MacOS Stealer”, this first came on the scene in mid-2024 as a “malware as a service” exploit.
-

NIST Cybersecurity Framework 2.0 – Considerations for Small to Medium Sized Businesses
The NIST Cybersecurity Framework is a methodology designed to simplify the process of planning, implementing, managing and responding to threats from a holistic point of view in the Information Technology Delivery and Security space. It is specifically designed for organizations that either have no or very little cybersecurity planning, processes or responses to emerging threats.
