AI Workflow Automation And Business Process Automation Services
Design, document, and automate the work that runs your business so it flows the same way, every time.
AI & Workflow Automation Services
From scattered tasks and manual rework to documented, automated workflows that support growth and compliance.
We work with platforms such as Microsoft Copilot, Power Automate, n8n and other automation tools, but we remain tool agnostic so the AI automation services we provide fit your systems, controls, and people.
What AI & Automation Change For Your Team
We help you move beyond one-off bots and scripts into intelligent automation solutions – reliable systems that free up capacity, improve accuracy, and make your operating model more predictable.
Process Discovery and Design
We map your current workflows, identify bottlenecks, and design a future state that reduces handoffs, errors, and rework while aligning with your controls.
Workflow Automation Integration Services
We connect the tools you already own so data moves cleanly between systems and the right people are notified at the right time.
Copilot and M365 Enablement
We help your team get real value from Microsoft Copilot and related tools by aligning prompts, governance, and digital workflow automation with your daily work.
Human-in-the-Loop Guardrails
We design approvals, reviews, and controls into your AI driven business automation so AI speeds up work without creating new risk.
Monitoring, Metrics, and Improvement
Dashboards and simple metrics show where AI process automation services save time and where the process still needs tuning — so you keep improving over time.
Compliance and Risk Aligned Automation
For regulated industries we align automations with exam expectations, documentation needs, and your cyber and data governance requirements.
Why TorchLight for AI Workflow Consulting Services?
At TorchLight, we believe AI workflow automation should make your business more predictable, not more chaotic. We focus on the systems that run your organization, then apply automation where it reduces noise and risk instead of creating new problems.
Our team blends IT, security, and AI business process automation expertise so your automations respect role-based access, audit requirements, and examiner expectations. We prioritize open communication and a partnership mindset so leaders stay in control of outcomes while we handle the technical details.
The result is a clear process automation strategy consulting roadmap, documented workflows, and automations that support your people. You gain capacity, consistency, and confidence that critical processes will run even when key staff are out of office.
Frequently Asked Questions
How does TorchLight help with AI Workflow Automation?
AI workflow automation covers the full journey from mapping your current processes to designing, building, and running automated systems that replace manual, error-prone steps. TorchLight helps with process discovery, tool selection, integration, guardrails, and ongoing improvement – so the result is a reliable operating model, not just a one-off script.
What platforms do you use for workflow automation services?
We work with Microsoft Copilot, Power Automate, n8n, and other leading platforms. Our approach to workflow automation services is tool-agnostic. We recommend the platform that fits your existing systems, security controls, and compliance requirements, not the one that’s easiest for us.
How do business process automation services work for regulated industries?
For regulated industries business process automation services require more than just connecting tools. We align every automation with your exam expectations, documentation standards, and data governance requirements – so the efficiency gains don’t create new compliance gaps.
Do you offer AI automation consulting before we commit to a full build?
Yes. We offer an Automation Assessment as a starting point. Our AI automation consulting engagement covers your current workflows, the biggest automation opportunities, the right tools for your environment, and a realistic roadmap – before any build work begins.
What is the difference between enterprise workflow automation and standard automation?
Enterprise workflow automation goes beyond simple task automation. It covers cross-department processes, multi-system integrations, compliance controls, role-based access, and governance – the kind of structure that regulated organizations and larger businesses need to scale automation safely.
How do you handle AI governance and human oversight in AI business automation solutions?
Every set of AI business automation solutions we build includes human-in-the-loop guardrails – approval steps, review checkpoints, and escalation paths that keep your team in control of outcomes. AI speeds up the work; your people remain accountable for the decisions.
What does intelligent workflow automation look like in practice?
Intelligent workflow automation means your systems don’t just move data — they make context-aware decisions. For example: routing an approval based on dollar threshold, flagging an anomaly for human review, or triggering a compliance documentation step automatically when a process milestone is reached.
Is TorchLight an AI automation services provider or a traditional IT firm?
Both. As an AI automation services provider with deep roots in IT and cybersecurity, TorchLight brings something most pure automation firms can’t: the ability to design automations that respect your security controls, compliance requirements, and IT infrastructure from day one.
Can you help with enterprise AI automation consulting for multi-department rollouts?
Yes. Our enterprise AI automation consulting engagements are designed for organizations rolling out automation across multiple teams or departments. We work with leadership, IT, and operations together to ensure the rollout is structured, documented, and aligned with your overall governance framework.
What are enterprise workflow automation services, and does TorchLight offer them?
Yes. Our enterprise workflow automation services cover end-to-end automation design, integration across business-critical systems, compliance alignment, and ongoing monitoring — built for organizations with complex environments, regulated processes, or multi-location operations.
Latest Insights & Blog
Expert insights on cybersecurity, compliance, and IT strategy.
-
Docusign Phishing Attacks Security Bulletin
The TorchLight Security Operations Center has seen a massive increase in fake Docusign phishing emails since Monday of this week. While these threat vectors has been in use since early 2024, the massive rise in attacks this week is real. At this point, consider all Docusign emails to be hostile and must be carefully reviewed…
-
The Palo Alto Paradox: Why Even Security Giants Fall Through Integration Gaps
Recently, Palo Alto Networks fell victim to a cyber-attack. Attackers used compromised OAuth tokens to breach 700+ organizations through a third-party marketing tool integration. If a security giant like Palo Alto can fall through integration cracks, what does that say about your exposure?
-

The Future of Authentication: Why Phishing-Resistant MFA Matters
MFA fatigue is creating security gaps as employees mindlessly click “approve” on authentication prompts. Learn how phishing-resistant MFA eliminates password frustration while stopping credential-based attacks entirely. Augusto Melo explores why this strategic shift cuts breach risk, boosts productivity, and positions organizations ahead of compliance requirements.
-
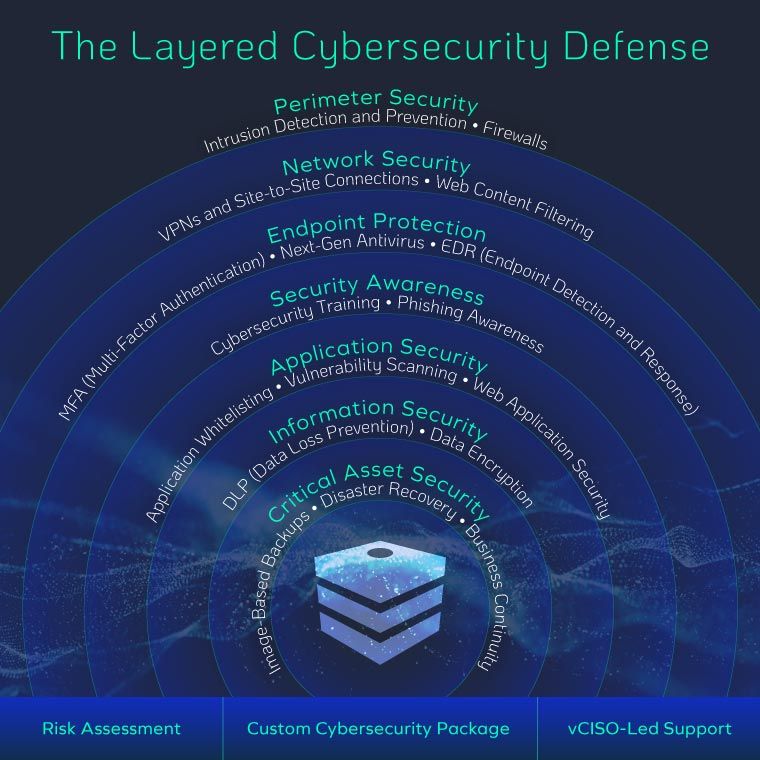
Why Advanced Cybersecurity Tools Still Fail – And What to Do Instead
It seems like every week another well-known company falls victim to a cyberattack – even those armed with the latest, most expensive cybersecurity tools. So why do breaches keep happening? After 15 years of breach investigations, one pattern is clear: most organizations lack a holistic approach to security. Tools are important, but without layered defenses…
-
Why We Partnered with Drip7 Security Awareness Training to Tackle the Real Cybersecurity Risk: People
TorchLight has partnered with Drip7 to strengthen human-focused cybersecurity training. Learn how this microlearning platform helps reduce human error, improve security awareness, and support a holistic cybersecurity strategy for your business.
-
20 Ways GenAI Will Reshape Cybersecurity and What It Means for Your Business
Generative AI is reshaping cybersecurity and changing the way businesses operate. In a recent Forbes Technology Council feature, TorchLight CEO Nolan Garrett shared how AI is improving threat detection and response while also introducing new risks, from deepfakes to automated reconnaissance. This post also looks at how AI is transforming industries beyond security, accelerating the…
-
IT Should Be More Than Just Fixing Computers
Learn why SMBs need more than basic IT support – and how a security-first MSP like TorchLight can protect your business from modern cyber threats.
-

“Among the Best They Have Ever Evaluated.”
When an independent auditor calls your security framework “among the best they’ve ever evaluated,” you know something’s working. At TorchLight, we deliver enterprise-grade IT and cybersecurity tailored to regulated small businesses – without the enterprise budget.
-

Is Your Small Organization Nearing a Cybersecurity Breaking Point?
Small businesses are facing a cybersecurity breaking point – strained IT teams, rising threats, and tight budgets. TorchLight delivers scalable, enterprise-grade protection tailored to your size and cost constraints.
-

Why Security-First Design Starts With Simplicity – Not More Controls
When cybersecurity becomes a barrier, people work around it – and that’s where risk begins. At TorchLight, we design security that aligns with your business, supports your users, and satisfies auditors – without slowing you down.
