
Stop Email Spoofing Before It Reaches Your Customers
Defend your brand, protect your customers, and cut the risk of phishing attacks by over 92%!
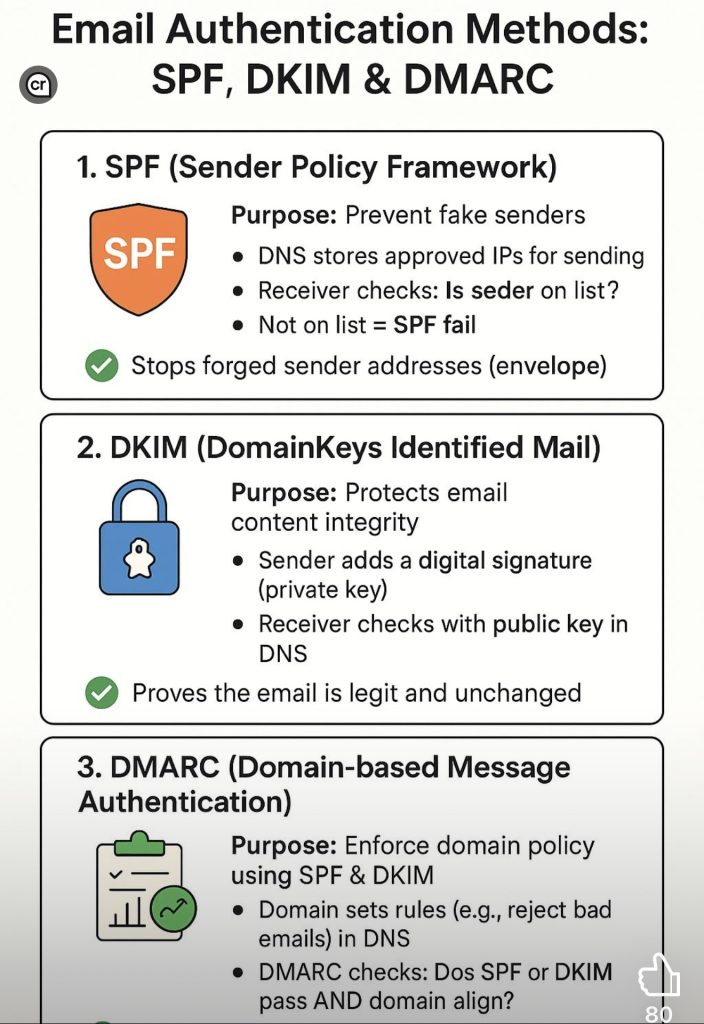
Why DMARC is essential for modern business email security
Every day, cybercriminals send millions of fraudulent emails that appear to come from legitimate businesses. These attacks damage customer trust, put your brand at risk, and can lead to financial and legal consequences.
DMARC (Domain-based Message Authentication, Reporting, and Conformance) is the industry standard for stopping these attacks before they reach inboxes. It works by verifying that emails sent from your domain are truly from you, blocking unauthorized senders, and giving you visibility into how your domain is being used.
Why DMARC matters:
Gives you actionable reports on domain activity
Protects your brand reputation
Blocks phishing and spoofing attempts
Increases email deliverability and trust
Gives you actionable reports on domain activity
Limited-Time Offer
For a limited time, get 50% off your DMARC service for the first 4 months when you sign up through this promotion.
Don’t wait until a phishing email damages your reputation. Secure your domain today and give your customers confidence that emails from you are legitimate.
Get Started and Claim 50% Off
The Way Forward – TorchLight Blog
-

Microsoft Teams Phishing Attacks
TorchLight Security Operations Center continues to hear about Microsoft Teams as the vector to social engineering, phishing and spearphishing attempts by hackers. Given the volume of noise, we thought we’d publish what we know and how to defend against these attacks.
-

New Mac Vulnerability – Banshee MacOS Stealer
Our security operations center was notified of a new and novel bug that can affect all Macs. Titled “Banshee MacOS Stealer”, this first came on the scene in mid-2024 as a “malware as a service” exploit.
-

NIST Cybersecurity Framework 2.0 – Considerations for Small to Medium Sized Businesses
The NIST Cybersecurity Framework is a methodology designed to simplify the process of planning, implementing, managing and responding to threats from a holistic point of view in the Information Technology Delivery and Security space. It is specifically designed for organizations that either have no or very little cybersecurity planning, processes or responses to emerging threats.
-

Industry Impact of Ransomware Attacks
Find out why academic institutions, automobile dealerships, and the utility sector are all high-profile targets of ransomware attacks.
-

Employee Training & Email Security
Find out why employee training is essential for maintaining email security and protecting your business.
-

What to Know About Email Security
One of the weakest links in keeping your business secure can be the employee who opens a malicious email. Attack vectors get more and more sophisticated every day. That is why having up-to-date email security should be a top priority for your business.
-

New NIST Guidelines Offer Starting Point for Cybersecurity
Important highlights about the National Institute of Standards and Technology (NIST) update of its guidance to organizations for assessing their internal security IT system.
-

Customer Testimonial: WETA
The proactive nature of the WETA’s leadership, spearheaded by Ken Jones (Senior Director, IT), drove WETA to form a partnership with TorchLight to ensure appropriate support for an infosec foundation as effective—and agile—as the ever-evolving threats and risks it faces.
-
Statement on Russia Cyberattacks
While we are aware of no specific or credible Russian cyber threats to the United States at this time, CISA recommends that organizations continue to be prepared to respond to any disruptive cyber activity.
-

Why Zero Trust is Essential for Remote Work
The rise of Zero Trust has helped businesses remain secure – even in remote working environments. Here are a few things that you should know about zero trust for your business and why it is essential for remaining cyber secure in both hybrid and remote workspaces.