Managed Security Services for Regulated Businesses
Get fully managed cyber security services with 24/7 monitoring, threat detection, and compliance-ready reporting, delivered by a trusted managed security service provider.
• Stop identity takeovers and invoice/payment fraud.
• Reduce ransomware exposure and contain incidents fast.
• Support audit and insurance requirements with clear reporting.
Managed Security Services Built for Regulated and Accountability-Driven Teams: Financial Services • Public Sector • Compliance-Sensitive SMBs
We’ll assess fit and the fastest risk-reduction path.
What Our Managed Security Services Include

SOC
(Security Operations Center) 24/7/365 monitoring
Our SOC delivers always-on monitoring through cyber security managed services. Analysts validate alerts, investigate threats, and coordinate response—providing enterprise-level protection without building an in-house team.

EDR
(Endpoint Detection & Response)
Detects suspicious activity on computers and can isolate compromised devices. Our advanced threat detection services at the endpoint level catch what traditional antivirus misses – behavioral anomalies, lateral movement, and fileless attacks.

ITDR
(Identity Threat Detection & Response)
Protect Microsoft 365 and identity systems from token abuse, risky logins, and unauthorized access through continuous monitoring included in our MSSP services, with real-time threat detection.

SIEM (Security Information & Event Management)
We aggregate and analyze signals across your environment to detect patterns and threats early, core to our cyber security managed services approach.

DMARC Monitoring
Prevent spoofing and impersonation attacks with continuous domain monitoring as part of our managed security services.

Vulnerability Management
Identify, prioritize, and remediate vulnerabilities before attackers exploit them, delivered through proactive managed cyber security services.
How Our Managed Security Service Responds to Threats
Security response shouldn’t be chaos. As a managed security service provider, we follow a repeatable process – every time, for every client.
Is Our Managed Security Service the Right Fit?
Identity attacks → ITDR • Endpoint threats → EDR • Email impersonation → DMARC • Pattern detection → SIEM
Built for Organizations That Need Managed Security Services Without Surprises
• Credit unions & community banks
• Wealth management, RIAs, family offices
• Municipalities & public-sector departments
• Compliance-sensitive SMBs (legal, CPA, professional services)
These industries share a common need: enterprise managed security services with the depth of a full in-house SOC – without the cost of building one.
If any of this is happening, Vigilance is a fit:
• Microsoft 365 account takeovers / risky logins
• Ransomware pressure + insurer/audit requirements
• Vendor sprawl + unclear ownership during incidents
• Need 24/7 monitoring without hiring a full SOC team
The Value of Managed Cyber Security Services
1) Early detection & rapid containment:
Validate alerts fast so small events don’t become major incidents.
2) Lower fraud and ransomware exposure:
Layered controls reduce both likelihood and impact.
3) Audit and insurance readiness:
Clear evidence and reporting for renewals and exams
4) Executive visibility (no jargon):
What happened, what changed, what was blocked, explained in business terms.
5) Peace of mind (24/7/365):
Always-on monitoring backed by humans.
Why Managed Security Services Work Better When IT Is Integrated
Most security incidents quickly become IT issues. When a single managed security service provider delivers both cyber security managed services and IT operations, response is faster, more coordinated, and more effective.
• Faster fixes: no waiting on third-party IT to patch or rebuild
• Cleaner containment: security actions align with device/user management
• One operating model: fewer gaps between “security” and “support”
Ask about a Stability + Vigilance bundle for full coverage.
Frequently Asked Questions
What is Managed Security?
Managed security services provide ongoing monitoring, detection, and response — so threats are handled continuously, not only after damage happens. Rather than reacting after a breach, a managed security service provider like TorchLight watches your environment 24/7/365 and acts the moment something suspicious is detected.
What’s included in Vigilance?
Vigilance typically includes 24/7/365 SOC monitoring, endpoint protection (EDR), identity protection (ITDR), and centralized visibility (SIEM). Add-ons may include vulnerability management and DMARC monitoring. Together, these form a comprehensive managed cybersecurity services stack – purpose-built for regulated environments.
What is a SOC and why does it matter?
A SOC (Security Operations Center) is a team of analysts who monitor your environment around the clock, validate alerts, and coordinate response. Our SOC as a service model gives businesses access to that level of coverage without the cost and complexity of building an internal SOC team. It’s one of the most effective ways to achieve continuous cyber threat monitoring without adding headcount.
Why isn’t antivirus enough?
Antivirus alone often misses modern threats – especially identity-based attacks and fileless malware. Effective managed SOC services layer detection across endpoints, identities, email, and network behavior, so attackers can’t hide in the gaps that antivirus leaves open.
What is EDR?
EDR watches for suspicious behavior on computers and helps stop malware and ransomware by isolating affected devices. It’s a core component of advanced threat detection services – catching threats that bypass signature-based tools by focusing on behavioral indicators.
What is ITDR?
ITDR helps protect Microsoft 365 identities and detects risky logins and suspicious access that can lead to fraud. It’s part of TorchLight’s network security monitoring services layer – covering the identity plane that traditional endpoint security often misses.
What is a SIEM?
A SIEM collects signals from security tools so patterns become visible – like “impossible travel” logins or multi-step attacks. In our managed SOC provider model, the SIEM is the central nervous system that gives our analysts the full picture across your environment.
What happens when you detect a threat?
We validate the alert, contain the issue, coordinate remediation, and provide a clear summary and recommended next actions.
Can you work with our internal IT team?
Yes. Vigilance can complement internal IT, or work best when paired with Stability for faster remediation.
Does this help with cyber insurance and audits?
It can. Our managed cyber security solutions include the reporting and evidence that supports compliance conversations and security control validation – making renewals and exam cycles significantly less stressful.
How long does onboarding take?
It depends on your environment and scope. We typically start with discovery, then deploy and tune controls, then move into steady-state monitoring
How does managed security services pricing work?
Managed security services pricing is typically per user per month and depends on which controls are included and your coverage needs. The final cost reflects the specific tools deployed – SOC, EDR, ITDR, SIEM, vulnerability management – and the size of your environment. The best way to get an accurate number is a 15-minute consultation where we assess your environment and recommend the right coverage level.
Why is it better to have IT + Security with one provider?
Because the response is faster and cleaner. Security events often require IT actions — patching, access changes, device remediation. One MSSP that also manages your IT removes the handoff delay and eliminates the finger-pointing that happens when two separate vendors share responsibility.
Why Choose TorchLight as Your Managed Security Service Provider
At TorchLight, our mission is simple: protect our clients and help them operate securely in an increasingly hostile threat landscape. As a trusted managed security service provider (MSSP), we deliver managed cyber security services designed to reduce risk, improve visibility, and support long-term business resilience.
We operate with candor, transparency, and proactive communication; partnering closely with organizations that value accountability and measurable outcomes. Unlike traditional cyber security managed services providers, we don’t just monitor alerts; we align security, IT operations, and response into a unified system that works in real-world environments.
Together, we ensure that IT security goals are not only met but exceeded, safeguarding business continuity every day. Our people are our greatest asset, unified by our mission to secure and serve our customers and frustrate the hackers.
Latest Insights & Blog
Expert insights on cybersecurity, compliance, and IT strategy.
-

“Among the Best They Have Ever Evaluated.”
When an independent auditor calls your security framework “among the best they’ve ever evaluated,” you know something’s working. At TorchLight, we deliver enterprise-grade IT and cybersecurity tailored to regulated small businesses – without the enterprise budget.
-

Is Your Small Organization Nearing a Cybersecurity Breaking Point?
Small businesses are facing a cybersecurity breaking point – strained IT teams, rising threats, and tight budgets. TorchLight delivers scalable, enterprise-grade protection tailored to your size and cost constraints.
-

Why Security-First Design Starts With Simplicity – Not More Controls
When cybersecurity becomes a barrier, people work around it – and that’s where risk begins. At TorchLight, we design security that aligns with your business, supports your users, and satisfies auditors – without slowing you down.
-

Why Small Businesses Are the New Cyber Targets – And How to Stay Protected
Cybercriminals target the vulnerable, not just the big guys. For small businesses in regulated industries, the risks are real – compliance gaps, lost trust, even financial collapse. At TorchLight, we make enterprise-grade cybersecurity practical and personal, with strategy-led protection built for your business.
-
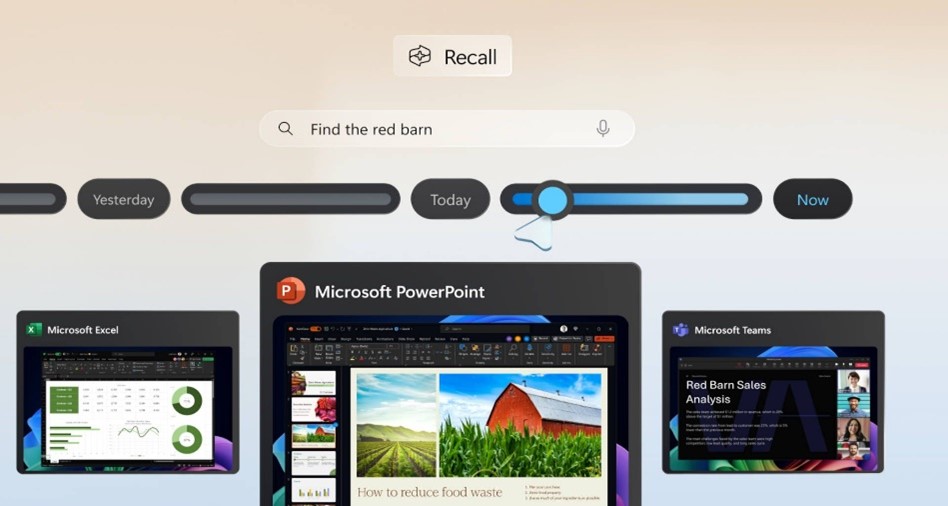
Windows Recall: What You Need to Know – And Why It Matters
Microsoft’s upcoming Recall feature for Windows 11 Copilot+ PCs is shaping up to be one of the most talked-about developments in workplace technology this year. Designed to boost productivity by taking periodic snapshots of user activity for easy, searchable recall, the feature promises convenience – but also raises serious privacy and security concerns.
-

Strengthening Your Security Posture with EDR & ITDR
Cyber attackers aren’t just targeting networks anymore – they’re going after identities and endpoints at scale. In fact, over 80% of breaches involve compromised credentials or exploited devices. In this month’s service spotlight, we break down two critical layers of modern cyber defense – Endpoint Detection and Response (EDR) and Identity Threat Detection and Response…
-

Washington State Expands Sales Tax to IT Services
A new Washington State law – Senate Bill 5814 – goes into effect on October 1, 2025, and it will significantly impact customers located in Washington who receive IT, digital, and tech-related services. This change will apply regardless of where the service provider is located, and may affect how your organization is billed by vendors…
-
The Windows 10 to Windows 11 Transition
Another large milestone looms in the Microsoft ecosystem as Windows 10 is (mostly) officially sunsetted on October 14, 2025. Meaning, no new security updates will be produced by Microsoft, unless you purchase an ESU/Extended Security Update license for up to three years that will allow Windows 10 to continue receiving security updates on a regular…
-
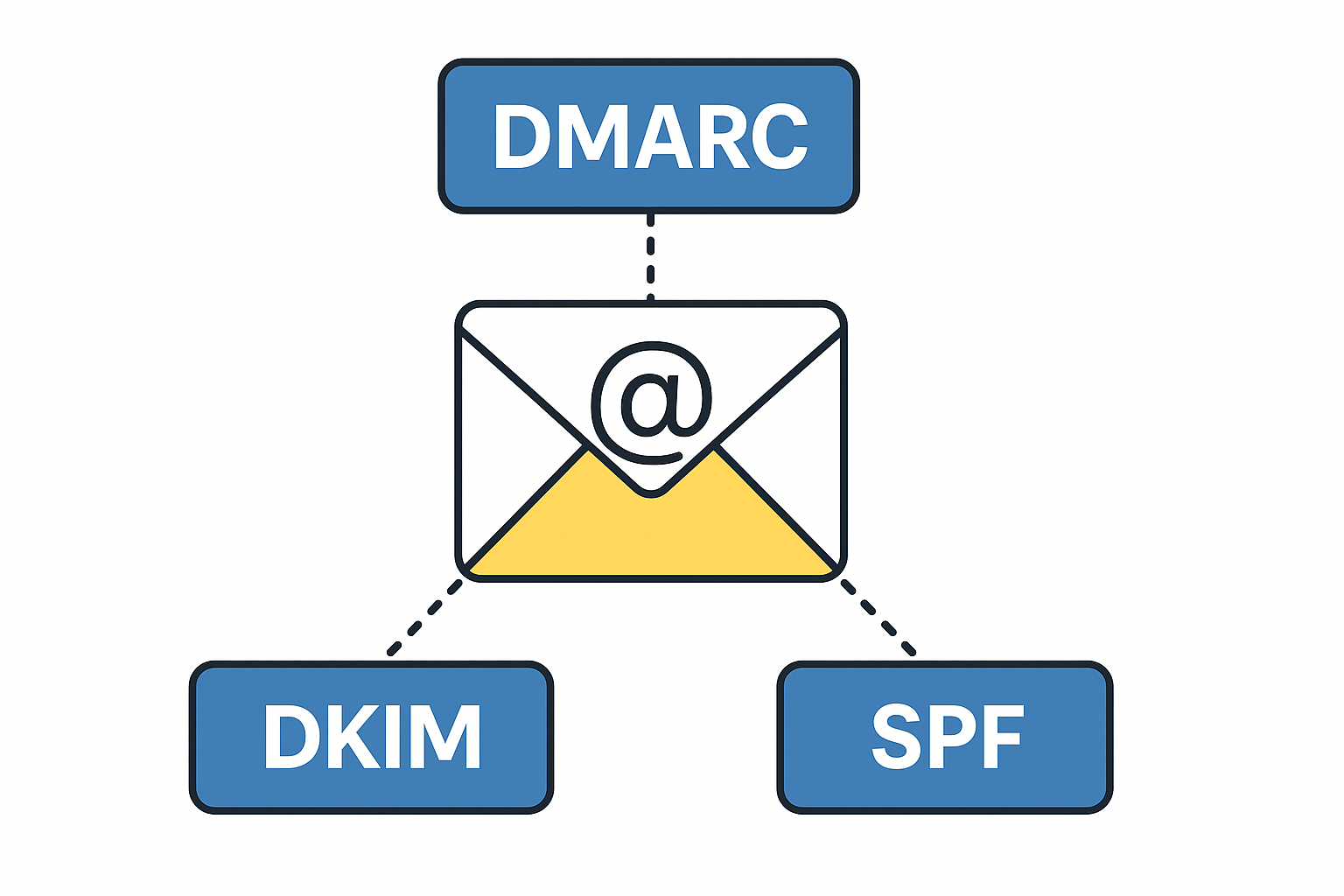
Tech Talk – What is DMARC, DKIM, SPF & Why Do I Want To Know?
DMARC, DKIM and SPF are three separate email authentication protocols that build layers of security around email delivery and integrity. Used in conjunction with each other, they provide a durable layer of protection for inbound emails and brand protection to prevent bad actors from sending emails using your business domain name. These tools provide domain…
-
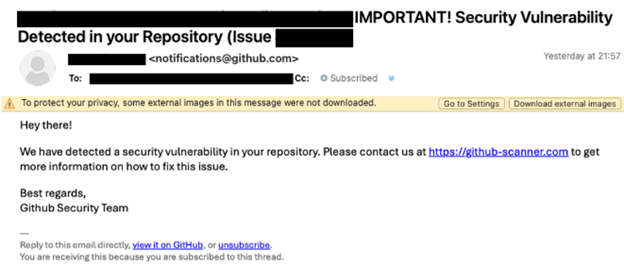
Beware of the ClickFix Scam!
TorchLight’s Threat Intelligence team has uncovered a resurgence of a phishing scam called ‘ClickFix,’ initially identified in late 2024 but now widely used by cybercriminals in 2025.
