Co-Managed IT & Security That Works Alongside Your Team
TorchLight partners with your internal IT staff, adding 24/7 monitoring, SOC threat detection, and senior engineering depth through a fractional model scaled for your organization.
- Works with your existing IT staff: no displacement, transitional downtime
- 24/7 NOC and SOC coverage your team can’t cost-effectively build alone
- One bill, one team, documented SLAs, starting at a fraction of a fully loaded IT hire
30 Minute
Critical incident response, 24/7/365
1
Bill, 1 vendor, 1 accountable partner
0
After-hours gaps in coverage
$80,000
Cost savings relative to a comparable internal team
Most Internal IT Teams Are Built for Helpdesk. Threat Detection, Security Operations, and Senior Engineering Are a Different Problem.
Your IT staff is good at keeping things running. They handle helpdesk tickets, onboard users, coordinate vendors, and keep the lights on. That’s exactly what they should be doing.
What they can’t do, and shouldn’t have to, is run a SIEM, manage threat intel feeds, maintain 24/7 SOC coverage, write compliance documentation, and be on call at 2 a.m. on a Saturday. That’s a structural mismatch, not a failure of your staff.
The fix is usually not another hire. Additional IT personnel typically cost $80,000–$110,000 per year per employee, bring one more point of failure, and still can’t replicate enterprise-grade monitoring and security operations. TorchLight does all of that, with a fractional pricing model that scales with your needs.
Network & Infrastructure Management
Proactive monitoring and management of switches, routers, firewalls, and wireless access points
- Server management for physical and virtual environments: updates, maintenance, patch management, and group policy
- 24/7/365 Network Operations Center (NOC) with active human monitoring
- Scalability planning to support business growth without adding headcount
- Server and workstation backup with cloud or bare metal restoration for production servers and critical workstations
Timely Detection and Response
Continuous threat detection, triage, and response across your entire environment
- 24/7/365 Security Operations Center (SOC) with real-time threat detection, triage, and response
- Threat intelligence and continuous monitoring for active and emerging threats
- Incident response and remediation for security events
- SIEM for log correlation and compliance documentation
Endpoint & Identity Protection
Active protection for every device, identity, and email in your organization
- Endpoint detection and response (EDR) for continuous monitoring, threat detection, and automated response across all endpoints
- Anti-virus and Windows OS patch management
- Incident response and remediation for security events
- Multi-Factor Authentication (MFA): protecting user access to applications and networks
Service Desk & Advisory
Tier 2/3 escalation support, dedicated technical advisor, and quarterly leadership reporting
- Tier 2 and Tier 3 service desk support – escalation-ready engineering behind your internal team’s frontline
- Assigned technical advisor and account team with regular check-ins and leadership reporting
- Microsoft 365 Tenant Partner management
Zero-Cost IT: a five-stage model designed to pay for itself
Organizations with internal IT are already carrying the fixed cost of a salary, but without the compliance specialization or engineering capacity to generate a return on that investment. When TorchLight layers 24/7 NOC and SOC coverage, SIEM, and Tier 2/3 engineering on top of your existing team, our model’s cost offset mechanisms activate: insurance premiums drop, downtime shrinks, executive time is recovered, and vendor sprawl gets eliminated.
Stage 1: Stability foundation
Consolidate vendors, stop financial leakage and establish baseline 24/7 monitoring.
Stage 2: Security Layer
EDR, identity threat detection, SIEM deployment, hardening aligned to regulatory demands and leadership expectations.
Stage 3: Compliance Accelerator
Build audit-ready evidence into daily operations. Control mapping for relevant industry standards. Walk into exams with documentation already organized.
Stage 4: Proof Point
Penetration testing, vulnerability assessments, vCISO/vCIO advisory. Board-ready quarterly reporting. Insurance documentation carriers accept.
Stage 5: Competitive Peak
IT becomes a strategic advantage. Cost offsets reach up to $1.2M annually through reduced downtime, reclaimed executive and internal IT productivity, eliminated tool duplication, and improved insurance and regulatory outcomes.
Where the offsets typically come from
- Reduced downtime and operational disruption
- Reclaimed executive and internal IT staff productivity
- Eliminated vendor sprawl and duplicated tools
- Improved cyber insurance outcomes through demonstrated controls

What Makes Us Different?
TorchLight emphasizes collaboration among leadership, IT, security, and vendors. Our team helps you proactively identify hidden risk, empower employees, and create a superior experience for your staff and executives, not just react to alerts.
“Before TorchLight, our IT was a mess. When we suffered a breach, our MSP made recovery difficult and made us feel the productivity loss from the attack for weeks after it happened. After partnering with TorchLight, our internal team has been able to focus on day-to-day work while they provide us with capabilities an in-house team could never deliver.”
– Beth Passmore, Director of IT, East Adams Rural Healthcare
What Changes When TorchLight Works Alongside Your Team
Internal IT Alone
- One person’s availability, offline nights, weekends, and whenever something else is on fire
- Threats found when someone notices something is wrong
- Limited capacity to manage and use security tools
- Escalations land on the same people that have to handle everything else
- IT is a fixed overhead cost with no mechanism to offset it
With TorchLight Co-Managed IT
- 24/7/365 NOC and SOC coverage with active human monitoring and documented response times
- Real-time detection, triage, and response so incidents are contained before they become outages
- EDR, SIEM, email security, and MFA deployed, monitored, and maintained as a managed layer
- Tier 2/3 engineering bench available on demand, so severe and urgent issues don’t tie up the entire pipeline
- IT investment generates measurable cost offsets across insurance savings, productivity increases, downtime reduction, and vendor consolidation
Why TorchLight?
Led by a former IS&T examiner, supported by a CISSP, CISA, and CISM-certified team.
At TorchLight, our “why” is simple: we exist to serve our customers and protect them from the relentless threat of hackers. This mission drives everything we do, setting us apart in the MSP landscape.
We foster a culture of candor, transparency, service, proactive communication and a growth mindset, all aimed at supporting our clients’ needs. We seek trusted partnerships with organizations that share our values, prioritizing open dialogue and a win/win mindset.
Together, we ensure that IT security goals are not only met but exceeded, safeguarding business continuity every day. Our people are our greatest asset, unified by our mission to secure and serve our customers and frustrate the hackers.
Frequently Asked Questions
Will TorchLight try to replace my IT staff?
No. Co-Managed IT is a partnership model, not a replacement model. Your team keeps doing what they’re best at. TorchLight adds the monitoring depth, security operations, and engineering capacity that a one- or two-person IT department can’t cost-effectively build alone. Most clients tell us their internal IT staff is relieved to finally have real backup.
How does TorchLight work with our existing IT staff?
Your internal team keeps doing what they do today – frontline support, user requests, on-site work. TorchLight sits behind them as the NOC, SOC, and Tier 2/3 engineering layer: monitoring your environment around the clock, catching threats before they become incidents, and handling escalations your team doesn’t have the tooling or bandwidth to cover. We integrate into your environment and your workflow – we don’t displace your team or compete with them.
What does co-managed IT typically cost?
It depends on the size and complexity of your environment. What we can say consistently: the model costs significantly less than adding an equivalent level of capability through full-time headcount. The assessment is the right place to get a number specific to your organization.
What does the onboarding process look like?
TorchLight provides the documentation, ticketing tools, and password management infrastructure from day one. The onboarding framework is designed to minimize friction for your internal team. Once fully onboarded, you receive a single consolidated monthly invoice covering all services.
How quickly do you respond when something goes wrong?
Contractual SLAs apply 24/7/365. Critical incidents receive a 30-minute first response from the NOC and a 15-minute first response from the SOC. Your internal team will always have a named point of contact, not a queue.
Can co-managed IT help with cyber insurance requirements?
Yes. Carriers increasingly require controls that internal IT teams can’t implement alone – EDR coverage, SIEM, documented incident response processes, patch management evidence. TorchLight’s co-managed model builds these controls into daily operations and produces the documentation carriers accept.
We already have a small IT team. Is there a minimum size requirement?
No minimum. The typical co-managed client has 1–3 internal IT staff and 50–250 employees. The model scales in both directions. If you have one IT generalist handling everything and a growing business, that’s exactly the situation co-managed IT was designed for.
What if we only need occasional engineering help?
TorchLight offers a block hour model for Tier 2/3 engineering access, starting at 5 hours per month. It’s a natural entry point for organizations not ready for a full co-managed engagement but who need periodic senior technical support without committing to a recurring contract.
When IT is boring, it’s not a liability. It’s your edge.
Your internal IT team is doing their best. The question is whether the infrastructure behind them is doing its best, too. Start with a free assessment. We’ll review your environment, map the gaps, and show you exactly what co-managed IT would look like for your organization.
Latest Insights & Blog
Expert insights on cybersecurity, compliance, and IT strategy.
-
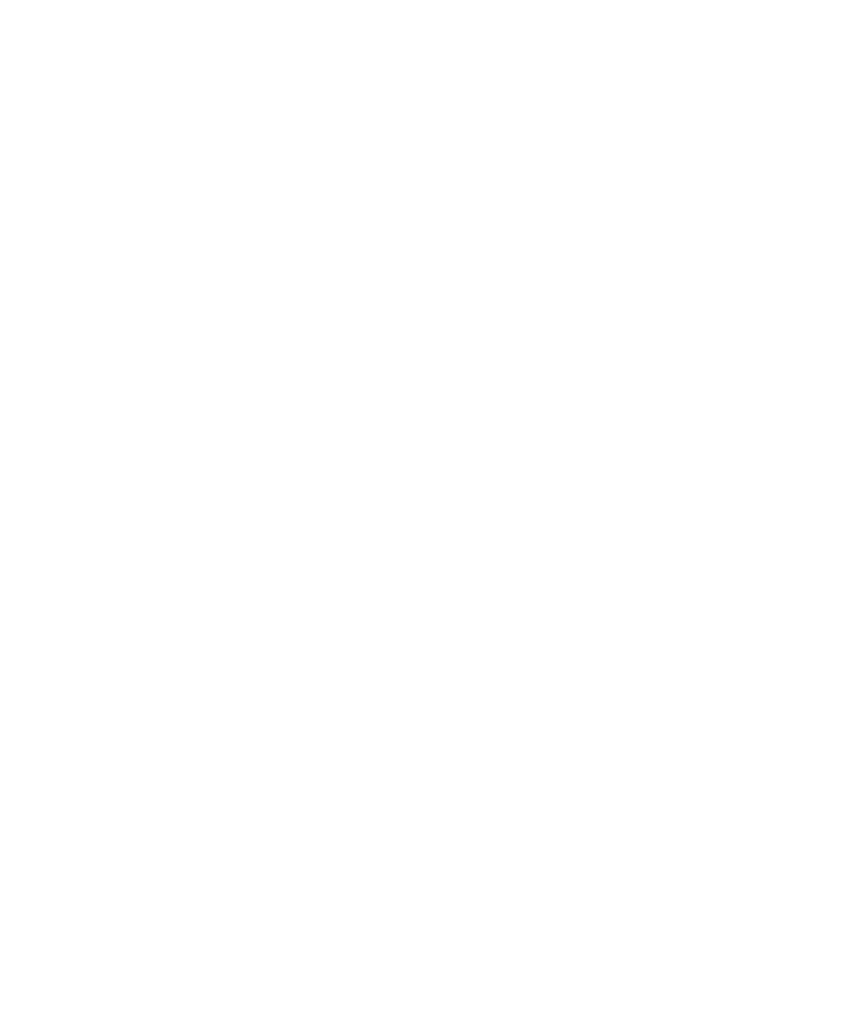
Three Days to Patch a 10.0: What The Cisco SD-WAN Vulnerability Says About Every Network in 2026
Two critical ScreenConnect vulnerabilities, including a CVSS 9.0 flaw under active exploitation by nation-state actors, have opened a direct tunnel into the networks of banks, RIAs, and healthcare practices. The federal patch deadline is May 12, 2026. Here’s what to check, what to hunt for, and how to close the door before examiners or attackers…
-
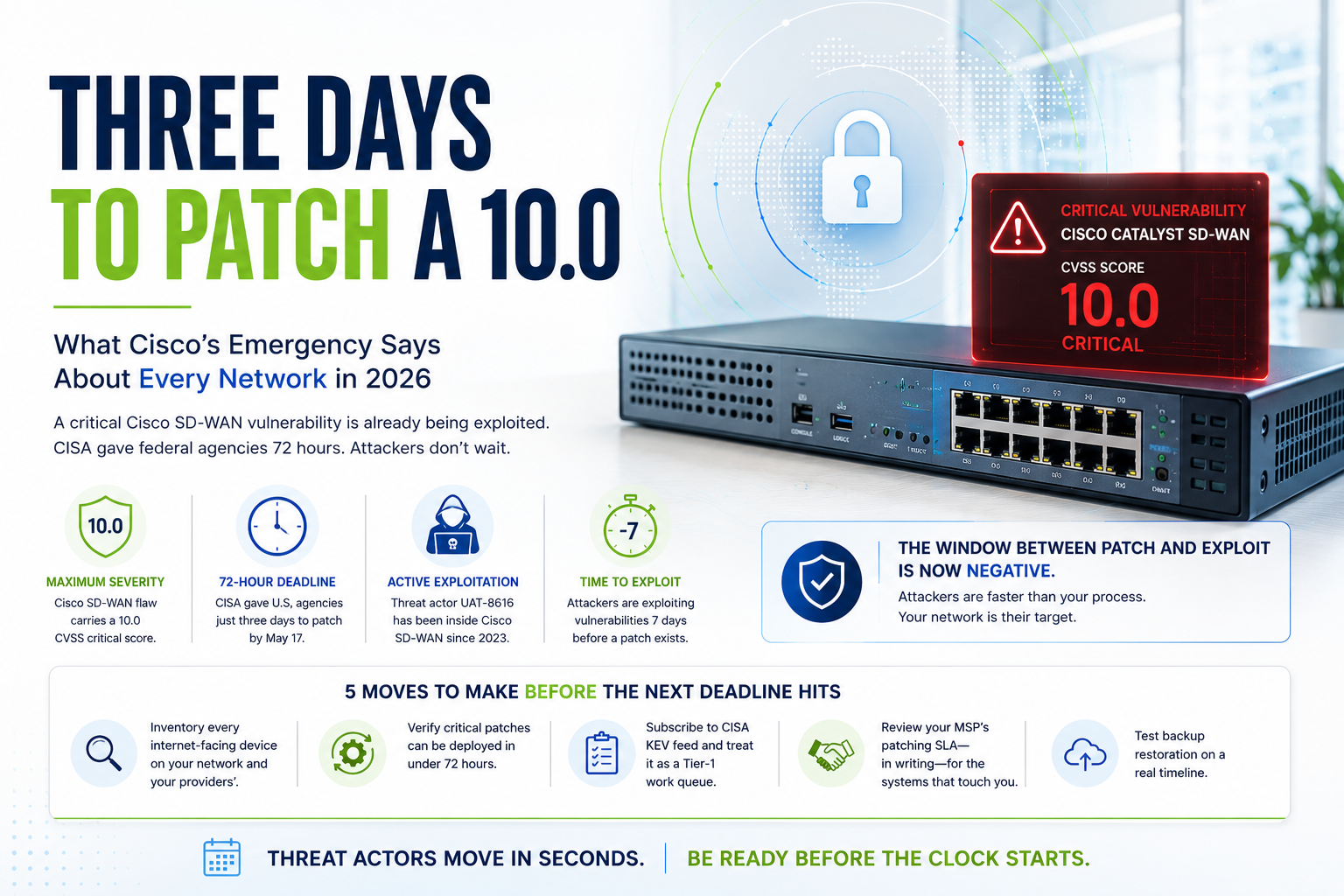
Staff Augmentation vs Managed Services: What IT Leaders Need to Know Before Choosing
Not long ago, the answer to an IT gap was simple: hire a contractor, bring in a temp resource, or extend a vendor engagement. Staff augmentation felt flexible, affordable, and fast. For many organizations, it still has a role to play. But the IT environment has changed dramatically. Ransomware attacks are targeting mid-market companies and…
-

Your Remote Access Tool Could Be Your Biggest Threat
Two critical ScreenConnect vulnerabilities, including a CVSS 9.0 flaw under active exploitation by nation-state actors, have opened a direct tunnel into the networks of banks, RIAs, and healthcare practices. The federal patch deadline is May 12, 2026. Here’s what to check, what to hunt for, and how to close the door before examiners or attackers…
