
Credit Union Compliance Confidence
How One Credit Union Went From Cyber Insurance Cancellation to Zero NCUA Cybersecurity Findings in 90 Days
The step-by-step transformation that eliminated emergency IT calls during member service hours and restored board confidence.
Cyber Insurance Canceled
TorchLight received a phone call from a Credit Union CEO facing a crisis. Their insurance company had just canceled coverage following a failed NCUA audit and ongoing technical issues that disrupted member services. The final straw came when their failing firewall caused operational downtime on a payroll Friday.
The board was asking tough questions, but the CEO had been constrained by limited budget approval. Within 90 days, TorchLight transformed their operations.
- Upgraded their network infrastructure for bulletproof reliability
- Integrated previously ignored M365 licenses into daily business operations, including Teams, Outlook, SharePoint, and OneDrive
- Resolved all outstanding NCUA audit issues
- Restored the Credit Union to an insurable state
Secured & Managed IT by TorchLight
Our Secured & Managed IT Brings Board Actualization Through Our Maslow Heirarchy of Needs Approach To Credit Union Compliance Confidence:
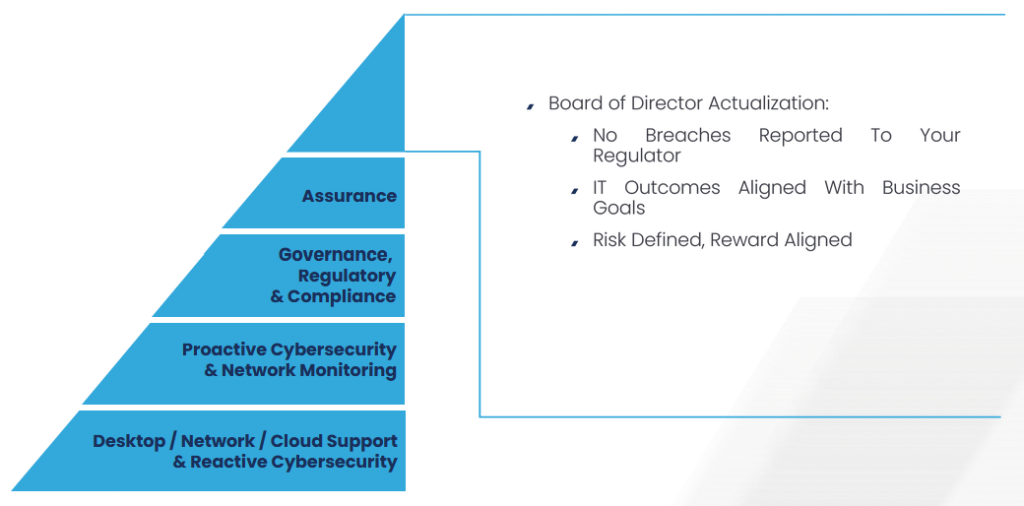
Board Actualization
- No Breaches To Report To Your Regulator
- IT Outcomes Aligned With Business Goals
- Risk Defined, Reward Aligned
Assurance
- Board Confidence That Controls And Oversight Actually Work
- If A Breach Were To Occur, Risk Communicated In Advance
- Act Swiftly To Recover, Contain Spread Immediately and Restore Operations Within Minutes
Governance, Regulatory and Compliance
- On Call Fractional Virtual Chief Information Security Officer
- Proactive Risk Awareness For Purpose Built Mitigations
- Board Level Reporting and Presentations By The vCISO
Proactive Cybersecurity and Network Monitoring
- 24/7/365 Human Powered Security & Network Operations Center
- DMARC, DNS and Email Spoofing Monitoring
- Desktop + Server Patching & Cloud + On-Prem Backups
- Customizable Security Awareness Training
- Dedicated Organizational Password Manager
- Integration with HR, Physical Access and Other Critical Systems
Desktop / Network / Cloud Support and Reactive Cybersecurity
- Patching + Backups
- Endpoint Detection + 24/7/365 Managed Incident Response
- Cloud Identity Detection + 24/7/365 Managed Incident Response
- Microsoft 365 Tenancy & License Management
- Predictable and Reliable Service Desk with Guaranteed SLA’s
What To Expect Working With TorchLight
Before: Downtime, user friction, customer headaches, technical debt, compliance dread.
After: Zero downtime, simplified business processes, increased compliance accountability with a predictable monthly budget.
We get Credit Unions. With more than 17 years of Managed Security & IT experience, along with testing, audits and consulting experience, we know what it takes to bring Board Self Actualization!
- Smooth on-boarding with a gradual implementation plan
- On Call vCISO to advise, consult and speak to your IT risks and help build Board awareness
- Predictable monthly cost that scales with confidence when it’s time to grow
- Maximize the value and full benefits with your M365 licensing
- Technical Liaison with your Processors, Integrators and Vendors
Get a Cybersecurity Compliance Assessment From a Certified Microsoft Solutions Partner for Security to Upgrade Your Credit Union to a Better Secured & Managed IT State with Compliance Confidence.
Why TorchLight?
At TorchLight, our “why” is simple: we exist to serve our customers and protect them from the relentless threat of hackers. This mission drives everything we do, setting us apart in the Secured and Managed IT landscape.
We foster a culture of candor, transparency, service, proactive communication and a growth mindset, all aimed at supporting our clients’ needs. We seek trusted partnerships with organizations that share our values, prioritizing open dialogue and a win/win mindset.
Together, we ensure that IT security goals are not only met but exceeded, safeguarding business continuity every day. Our people are our greatest asset, unified by our mission to secure and serve our customers and frustrate the hackers.
Latest Insights & Blog
Expert insights on cybersecurity, compliance, and IT strategy.
-

Microsoft Defender vs Traditional Security Tools: What Actually Wins?
Every organization running Microsoft 365 faces the same question eventually: is the security baked into our Microsoft subscription actually protecting us — or are we spending money on tools we’ve already paid for while leaving real gaps open? It’s a fair question. And if you’re in a regulated industry — a credit union, a healthcare…
-
The AI That’s Too Dangerous to Release (And What It Means for Your Business)
A few weeks ago, Anthropic accidentally left nearly 3,000 unpublished internal files exposed on the public internet, no password required. Among those files was a draft blog post describing what the company called “by far the most powerful AI model we’ve ever developed.”
-
Google Proposed Device Bound Session Credentials To Prevent Session Theft – Will This Solve The Problem?
Google just rolled out something called Device Bound Session Credentials — DBSC for those who enjoy acronyms. But like most things that arrive wrapped in a press release, it’s worth taking a closer look before you decide whether to applaud or raise an eyebrow.
-
AV vs EDR vs MDR vs ITDR — What Regulated Organizations Actually Need
The Cybersecurity Tool Problem No One Talks About Here’s a conversation that happens more often than it should in boardrooms across financial services, healthcare, and government sectors: “Do we have antivirus?” the executive asks. “Yes,” the IT manager confirms. “Then we’re protected, right?” “…Sort of.” That “sort of” is where data breaches live. That hesitation…
-
Microsoft Defender vs Traditional Security Tools: What Actually Wins?
Every organization running Microsoft 365 faces the same question eventually: is the security baked into our Microsoft subscription actually protecting us — or are we spending money on tools we’ve already paid for while leaving real gaps open? It’s a fair question. And if you’re in a regulated industry — a credit union, a healthcare…
-
How to Build an Annual IT Budget: A Practical Guide for Regulated Organizations
Key Takeaways: Introduction: The Stakes of IT Budgeting in 2026 For leadership teams in regulated industries—financial services, healthcare, government, or higher education—an IT budget is far more than a spreadsheet of hardware costs. It is a strategic roadmap for risk management and operational continuity. In the 2026 threat landscape, a poorly planned budget doesn’t just…
-
How to Choose the Right IT Partner: A Buyer’s Guide for Compliance-Sensitive Organizations
Key Takeaways Before diving into the full guide, here are the essential criteria for selecting a partner in a high-stakes, regulated environment: In 2026, the stakes for business technology have never been higher. For leaders in regulated industries—financial services, healthsvcare, and government—the search for an IT partner is no longer about finding someone to “fix…
-

The After-Hours Threat Credit Unions Can’t Ignore
Cyber threat actors target credit unions when their staff aren’t looking. Here’s what two high-profile breaches reveal about attacker timing, and how small IT teams can close the coverage gap.
-

The Clock Is Ticking: What the June 3 Reg S-P Deadline Means For Smaller RIAs
The SEC’s amendments to Regulation S-P start applying to RIAs managing under $1.5 billion on June 3rd. Is your data security posture ready?
-

How AI Is Making Phishing Attacks More Dangerous, More Convincing, and Harder to Spot
AI has made phishing attacks so convincing and common that credit unions can no longer rely on employee vigilance alone to stop them.