Continuous Vulnerability Monitoring
Always-on visibility into your security posture, not just an annual snapshot.
Your Pen Test Shows Vulnerabilities Today. What About Tomorrow?
Penetration testing gives you a point-in-time assessment. But threats don’t wait for your next annual test.
New vulnerabilities are discovered daily. Configurations drift. Systems get added. Patches get missed.
Between pen tests, you’re flying blind.
The Solution: Continuous Vulnerability Monitoring from TorchLight
Cloud-based monitoring across all your connected endpoints. Get continuous security monitoring with regular reporting on discovered vulnerabilities, configuration issues, and risk-based prioritization.
Your always-on security radar between pen tests.
What You Get
Continuous Vulnerability Assessment
Automated scanning to identify security weaknesses as they emerge.
Configuration Monitoring
Track configuration drift and misconfigurations that create security gaps.
Risk-Based Prioritization
We prioritize based on criticality and your specific environment.
Regular Reporting
Vulnerability reports on your designated schedule with criticality ratings and clear remediation guidance.
Ideal for organizations that:
✓ Conduct annual or quarterly pen testing but need visibility between tests
✓ Need continuous monitoring for compliance or insurance requirements
✓ Want to identify and remediate vulnerabilities proactively
✓ Need ongoing security posture assessment alongside threat monitoring

Why TorchLight
Real People Who Care – Context, guidance, and support, not just automated reports
Security Expertise – Certified professionals (CISSP, OSCP, PCIP) who understand what matters
Compliance-Ready – Reports designed to support audit, insurance, and regulatory requirements
Proactive Protection – Find and fix vulnerabilities before attackers exploit them
Ready To Add Continuous Vulnerability Monitoring?
Latest Insights & Blog
Expert insights on cybersecurity, compliance, and IT strategy.
-
Why We Partnered with Drip7 Security Awareness Training to Tackle the Real Cybersecurity Risk: People
TorchLight has partnered with Drip7 to strengthen human-focused cybersecurity training. Learn how this microlearning platform helps reduce human error, improve security awareness, and support a holistic cybersecurity strategy for your business.
-
20 Ways GenAI Will Reshape Cybersecurity and What It Means for Your Business
Generative AI is reshaping cybersecurity and changing the way businesses operate. In a recent Forbes Technology Council feature, TorchLight CEO Nolan Garrett shared how AI is improving threat detection and response while also introducing new risks, from deepfakes to automated reconnaissance. This post also looks at how AI is transforming industries beyond security, accelerating the…
-
IT Should Be More Than Just Fixing Computers
Learn why SMBs need more than basic IT support – and how a security-first MSP like TorchLight can protect your business from modern cyber threats.
-

“Among the Best They Have Ever Evaluated.”
When an independent auditor calls your security framework “among the best they’ve ever evaluated,” you know something’s working. At TorchLight, we deliver enterprise-grade IT and cybersecurity tailored to regulated small businesses – without the enterprise budget.
-

Is Your Small Organization Nearing a Cybersecurity Breaking Point?
Small businesses are facing a cybersecurity breaking point – strained IT teams, rising threats, and tight budgets. TorchLight delivers scalable, enterprise-grade protection tailored to your size and cost constraints.
-

Why Security-First Design Starts With Simplicity – Not More Controls
When cybersecurity becomes a barrier, people work around it – and that’s where risk begins. At TorchLight, we design security that aligns with your business, supports your users, and satisfies auditors – without slowing you down.
-

Why Small Businesses Are the New Cyber Targets – And How to Stay Protected
Cybercriminals target the vulnerable, not just the big guys. For small businesses in regulated industries, the risks are real – compliance gaps, lost trust, even financial collapse. At TorchLight, we make enterprise-grade cybersecurity practical and personal, with strategy-led protection built for your business.
-
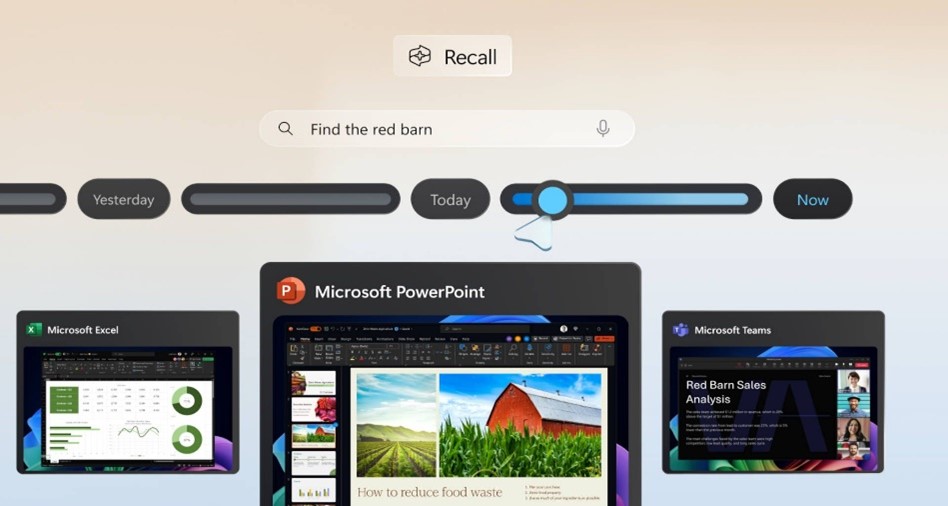
Windows Recall: What You Need to Know – And Why It Matters
Microsoft’s upcoming Recall feature for Windows 11 Copilot+ PCs is shaping up to be one of the most talked-about developments in workplace technology this year. Designed to boost productivity by taking periodic snapshots of user activity for easy, searchable recall, the feature promises convenience – but also raises serious privacy and security concerns.
-

Strengthening Your Security Posture with EDR & ITDR
Cyber attackers aren’t just targeting networks anymore – they’re going after identities and endpoints at scale. In fact, over 80% of breaches involve compromised credentials or exploited devices. In this month’s service spotlight, we break down two critical layers of modern cyber defense – Endpoint Detection and Response (EDR) and Identity Threat Detection and Response…
-

Washington State Expands Sales Tax to IT Services
A new Washington State law – Senate Bill 5814 – goes into effect on October 1, 2025, and it will significantly impact customers located in Washington who receive IT, digital, and tech-related services. This change will apply regardless of where the service provider is located, and may affect how your organization is billed by vendors…
