About Us
The IT Partner Regulated Organizations Needed Didn’t Exist, So We Built It
In January 2007, Nolan Garrett founded Intrinium with a clear mission: to provide IT and security services designed specifically for organizations that couldn’t afford to get compliance wrong.
After years working with credit unions, financial institutions, and other regulated organizations, Nolan saw the same pattern repeated: businesses were choosing between generic IT providers who didn’t understand regulatory requirements, or expensive consultants who only showed up when something was already broken. Neither option gave leadership the visibility, accountability, or proactive support they needed to stay ahead of examiners, auditors, and evolving threats.
Intrinium was built to solve that problem. From day one, the focus was on regulatory compliance, continuous risk management, and delivering outcomes that leadership could defend to boards, examiners, and insurance carriers. Not just technical competence, but business alignment.
That foundation, security-first managed IT designed for regulated and mission-critical environments, has guided every decision, acquisition, and service expansion since.
The Rebrand: Intrinium Becomes TorchLight
In 2021, Intrinium rebranded its operations to TorchLight. The people, expertise, and client relationships remained unchanged. What changed was the alignment between the brand and what clients actually valued: clarity, accountability, and illumination of cyber risk in an industry often characterized by complexity and vendor finger-pointing.
The name TorchLight reflects the company’s role as the source of truth for organizations navigating cybersecurity, compliance, and IT risk. Not just a vendor, but a partner capable of cutting through noise and delivering the visibility leadership needs to make confident decisions.
Growth Through Expertise, Not Just Scale
Intrinium grew rapidly in its early years, working with financial institutions across the Pacific Northwest and eventually across the United States. As demand increased, the business evolved into three distinct service lines:
- Managed IT Services: Proactive infrastructure management, service desk support, and operational continuity for organizations that couldn’t tolerate downtime or compliance gaps.
- Managed Security Services: Continuous monitoring, threat detection, and incident response tailored to regulated industries where breaches trigger regulatory notifications and reputational damage.
- Professional Services: Audit support, penetration testing, compliance assessments, and advisory services that help leadership demonstrate due diligence and pass examinations with confidence.
In 2010, Intrinium acquired Olympia Computer Central, establishing a presence in Washington’s state capital and expanding service delivery capabilities across the state.
Strategic acquisitions followed. In 2014, Intrinium acquired Interlink Advantage in Spokane, and in 2016, Contineo, a regional IT provider serving the Northwest. These weren’t acquisitions for scale. Each acquisition brought specialized expertise, client relationships in regulated industries, and teams aligned with the mission: deliver security and compliance as operational outcomes, not afterthoughts.
Trusted by Organizations Where Security and Compliance Are Non-Negotiable
Over the years, TorchLight’s client base expanded across industries where regulatory scrutiny, operational reliability, and stakeholder trust are foundational.
Government and Public Sector:
TorchLight has supported critical infrastructure and government operations across the United States, including work with the U.S. Capitol, and many Washington State agencies such as the Department of Revenue, Department of Licensing, and the Courts system. For over a decade, TorchLight has been a trusted provider on the Washington State Information Technology Professional Services (ITPS) contract, enabling public institutions to engage qualified IT and security expertise quickly without navigating complex procurement processes.
Financial Services:
From community credit unions to wealth management firms and family offices, TorchLight serves organizations where a single compliance misstep or security incident can trigger regulatory findings, insurance complications, or loss of client trust. Many large investment firms and high-net-worth family offices rely on TorchLight as their trusted IT and security partner, valuing the combination of technical rigor and discretion required in high-privacy environments.
Healthcare and Senior Services:
Between 2012 and 2013, TorchLight expanded heavily into healthcare, becoming the partner of choice for organizations such as Kootenai Health, Verity Health System, Children’s Hospital Los Angeles, Pipeline Health, and Logan Health. More recently, TorchLight has supported senior living and assisted care providers including Riverspring and Elderserve At Home, where operational continuity, HIPAA compliance, and protecting resident data are critical.
Higher Education:
In 2018, TorchLight was selected by the California Community Colleges Chancellor’s Office to provide GLBA risk assessments, ransomware risk evaluations, and security and penetration testing across all 120+ colleges in the system. This engagement required the ability to assess risk at scale, deliver actionable findings, and support institutions with varying technical maturity, all while meeting strict regulatory timelines.
Beyond Regulated Industries:
TorchLight also serves municipalities, retail organizations, and energy sector clients in oil and gas, all environments where operational downtime, data exposure, or security incidents carry significant business and reputational consequences.
Service Capabilities Built for Organizations That Can’t Afford Surprises
TorchLight’s service catalog reflects the needs of leaders who must balance operational demands, regulatory expectations, and limited internal IT resources.
Managed IT Services:
Proactive infrastructure management, help desk support, and IT operations designed to reduce executive involvement in day-to-day issues while maintaining visibility into risk and performance. TorchLight manages environments ranging from small deployments to organizations with 1,500+ seats, delivering consistent service quality regardless of scale.
Managed Security Services (SOC):
24/7/365 security operations center monitoring, threat detection, and incident response. TorchLight’s SOC provides continuous visibility into your environment, detecting compromised credentials, unusual access patterns, and emerging threats before they escalate into incidents that require board notifications or regulatory filings.
Endpoint Detection and Response (EDR):
Advanced threat protection across every device in your environment. EDR goes beyond traditional antivirus to identify, investigate, and neutralize sophisticated attacks that bypass signature-based defenses, a capability increasingly expected by examiners and cyber insurance carriers.
Identity Threat Detection and Response (ITDR):
Monitors for compromised credentials, suspicious authentication activity, and identity-based attacks that exploit your most privileged accounts. As identity becomes the primary attack vector, ITDR provides the visibility and response capability required to protect administrative access and meet regulatory expectations for access control.
Security Information and Event Management (SIEM):
The SIEM integrates signals from various cloud and on premise appliances and puts this data into one place which allows for rapid analysis, correlation and detection of analogous events. By correlating events in real time and applying advanced analytics, a SIEM turns massive volumes of raw data into actionable alerts, helping you identify suspicious activity before it becomes an incident.
DMARC Monitoring and Email Security:
Stops email impersonation attacks before they reach your team or stakeholders. DMARC monitoring validates every email claiming to be from your domain and provides visibility into who’s attempting to spoof your organization, protecting brand reputation and preventing business email compromise.
Security Awareness Training:
Realistic, engaging training that turns employees into active threat-spotters. TorchLight’s security awareness programs use simulated phishing, bite-sized learning modules, and measurable behavior change tracking to reduce human-related security incidents and demonstrate training effectiveness to auditors.
Virtual Chief Information Security Officer (vCISO):
Strategic security leadership without the cost of a full-time executive hire. TorchLight’s vCISO services provide board-level security guidance, risk assessments, policy development, and examiner preparation for organizations that need executive security expertise but don’t require it full-time.
Penetration Testing and Vulnerability Scanning:
Independent security testing that identifies exploitable weaknesses before attackers do. TorchLight’s penetration testing services satisfy examiner requirements, support insurance renewals, and provide leadership with evidence of proactive risk management.
Audits and Assessments:
TorchLight’s independent penetration testing and vulnerability scanning identifies exploitable weaknesses before attackers do, satisfying examiner requirements, supporting insurance renewals, and providing leadership with clear evidence of proactive risk management. With continuous vulnerability scanning and routine penetration testing, you’re not just checking a compliance box, you are closing the gaps that cybercriminals count on.
Network Operations Center (NOC):
Continuous infrastructure monitoring, performance management, and proactive patch management and maintenance to prevent outages and maintain operational continuity. TorchLight’s NOC ensures systems remain available, particularly during after-hours periods when internal teams aren’t monitoring.
Service Desk and Help Desk Support:
Responsive, knowledgeable technical support that reduces downtime and keeps teams productive. TorchLight’s service desk operates as an extension of your organization, providing consistent support quality and reducing the burden on operations managers who would otherwise be first-call troubleshooters.
Why Clients Choose TorchLight: Outcomes Over Outputs
TorchLight’s leadership, starting with CEO Nolan Garrett, has always focused on one question: does this help the client reduce risk, avoid surprises, and make better decisions?
Nolan’s background in computer science and security gives him a practical understanding of how systems actually fail, but what defines his leadership is how that knowledge gets applied. Under his guidance, TorchLight has grown around a principle that security should support the business, not slow it down, and IT should create clarity, not complexity.
For the leaders TorchLight works with, CEOs preparing for board questions, COOs frustrated by after-hours operational chaos, and Operations Managers exhausted by constant IT fire drills, this shows up in tangible ways:
- Fewer vendors to manage, with unified accountability when issues arise
- Clear priorities instead of endless alerts and competing technical recommendations
- A model designed to recover executive time and bring predictability to cost, risk, and outcomes
TorchLight’s Zero-Cost IT Model and advisory-led approach reflect Nolan’s belief that strong security is not about buying more tools or maintaining a wide bench of talent, but about aligning people, process, and technology around what actually matters: protecting stakeholder trust, passing examinations, and maintaining operational continuity.
Experience That Translates Across Industries
TorchLight’s team maintains a wide range of certifications and specializations, including CISSP, CISA, CISM, CRISC, and others that reflect deep technical competence and regulatory knowledge. More importantly, the team has experience across industries, markets, and business sizes within those markets.
Whether supporting a small credit union through a Microsoft 365 migration or leading a full-scale cybersecurity transformation for a multi-site healthcare system, TorchLight brings the same approach: security-first, risk-managed IT partnerships designed to deliver outcomes leadership can defend.
Organizations choose TorchLight not because they need another IT vendor, but because they need a partner who understands what’s at stake when compliance, operations, and stakeholder trust are on the line.
Latest Insights & Blog
Expert insights on cybersecurity, compliance, and IT strategy.
-

Your Remote Access Tool Could Be Your Biggest Threat
Two critical ScreenConnect vulnerabilities, including a CVSS 9.0 flaw under active exploitation by nation-state actors, have opened a direct tunnel into the networks of banks, RIAs, and healthcare practices. The federal patch deadline is May 12, 2026. Here’s what to check, what to hunt for, and how to close the door before examiners or attackers…
-

Managed IT Services Pricing in 2026: A Complete Guide for Businesses
When businesses start researching managed IT services, one question usually comes first: “How much should managed IT actually cost?” And honestly, the answers online can feel confusing. One provider may quote a few hundred dollars per month, while another charges thousands for seemingly similar services. Some include cybersecurity, backups, and cloud management in their pricing,…
-
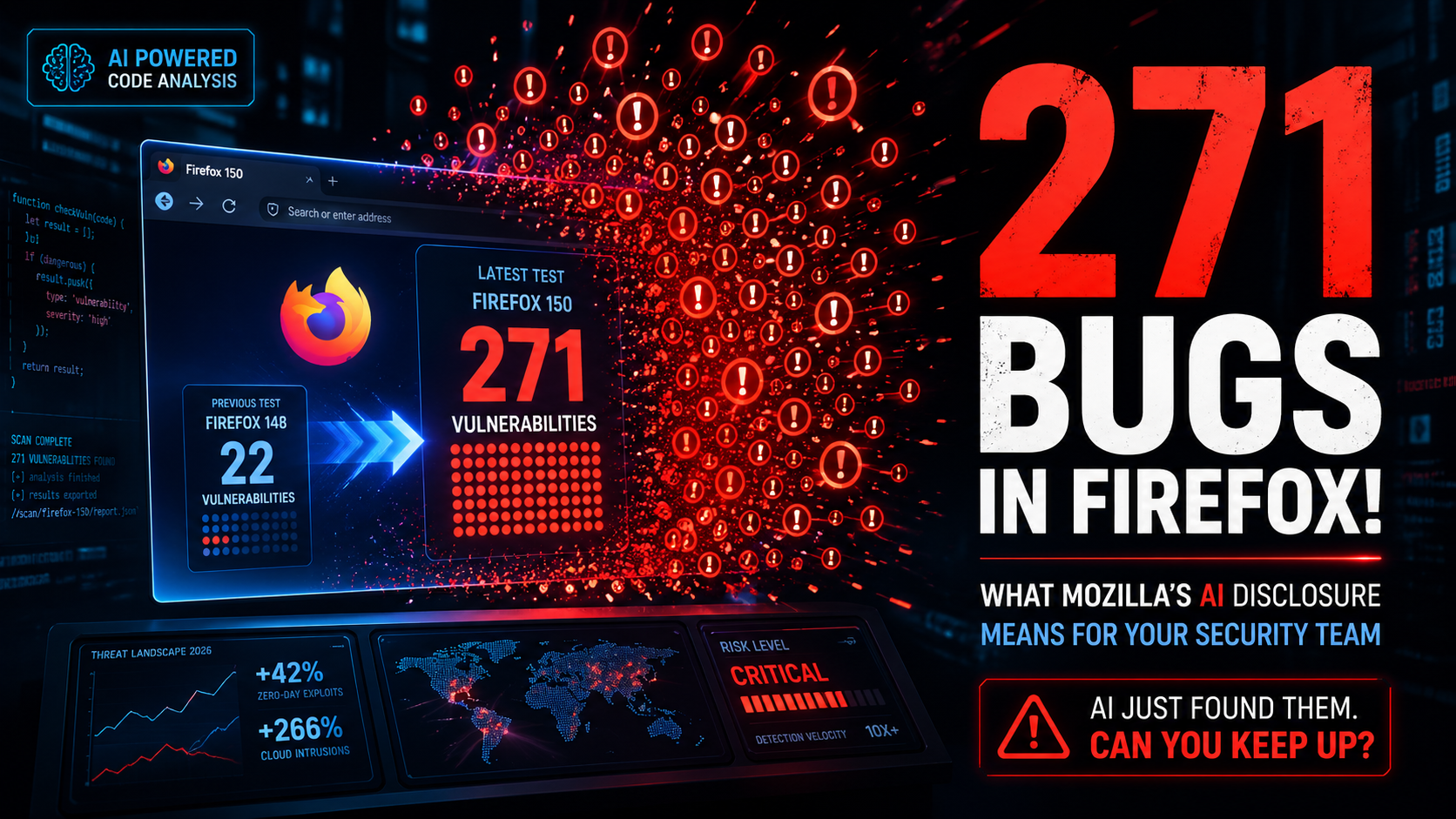
271 Bugs in Firefox! What Mozilla’s AI Disclosure Means for Your Security Team
Surfacing 22 new bugs in Firefox 148 was already an outlier. Surfacing 271 in Firefox 150 was something else entirely.
-

AI Phishing Attacks in 2026: Why Regulated Organizations Are at Risk
Phishing volume and sophistication have surged in 2026, driven by generative AI that lets attackers produce flawless, personalized lures at scale. Traditional email filters and “spot the typo” training can’t keep up.
-

Why Regulated Businesses Need Managed Security Services (MSSP) in 2026?
Executive Summary Managed Security Services Providers (MSSPs) deliver 24/7 threat monitoring, detection, and response capabilities that most organizations can’t build cost-effectively in-house. For regulated industries—credit unions, healthcare providers, government agencies, and wealth management firms—MSSPs have evolved from optional vendors to strategic necessities. This comprehensive guide explains what MSSPs actually do, who needs them, how to…
-
AV vs EDR vs MDR vs ITDR: What Regulated Organizations Actually Need in 2026
The Cybersecurity Tool Problem No One Talks About Here’s a conversation that happens more often than it should in boardrooms across financial services, healthcare, and government sectors: “Do we have antivirus?” the executive asks. “Yes,” the IT manager confirms. “Then we’re protected, right?” “…Sort of.” That “sort of” is where data breaches live. That hesitation…
-

Microsoft Defender vs Traditional Security Tools: What Actually Wins?
Every organization running Microsoft 365 faces the same question eventually: is the security baked into our Microsoft subscription actually protecting us — or are we spending money on tools we’ve already paid for while leaving real gaps open? It’s a fair question. And if you’re in a regulated industry — a credit union, a healthcare…
-
The AI That’s Too Dangerous to Release (And What It Means for Your Business)
A few weeks ago, Anthropic accidentally left nearly 3,000 unpublished internal files exposed on the public internet, no password required. Among those files was a draft blog post describing what the company called “by far the most powerful AI model we’ve ever developed.”
-
Google Proposed Device Bound Session Credentials To Prevent Session Theft – Will This Solve The Problem?
Google just rolled out something called Device Bound Session Credentials — DBSC for those who enjoy acronyms. But like most things that arrive wrapped in a press release, it’s worth taking a closer look before you decide whether to applaud or raise an eyebrow.
-
How to Build an Annual IT Budget: A Practical Guide for Regulated Organizations
Key Takeaways: Introduction: The Stakes of IT Budgeting in 2026 For leadership teams in regulated industries, such as financial services, healthcare, government, or higher education, an IT budget is far more than a spreadsheet of hardware costs. It is a strategic roadmap for risk management and operational continuity. In the 2026 threat landscape, a poorly…
