What Others Have To Say
We work hard to make happy customers – read these testimonials from our satisfied partners
Testimonials
“TorchLight has been more than a vendor to our multi-branch Credit Union, they are more like our partner. Our relationship with TorchLight dates back to 2007 when we were one of their very first clients who worked with them on a security assessment and gap analysis. TorchLight has worked with us ever since to help us achieve success for its employees and members through technology. They continue to strategically align with us to provide a full suite of services and have continued to deliver for almost 20 years.”
– Annettee Babb, CEO, PrimeSource Credit Union
Read more about how TorchLight’s credit union security expertise delivers
Why TorchLight?
At TorchLight, our “why” is simple: we exist to serve our customers and protect them from the relentless threat of hackers. This mission drives everything we do, setting us apart in the Secured and Managed IT landscape.
We foster a culture of candor, transparency, service, proactive communication and a growth mindset, all aimed at supporting our clients’ needs. We seek trusted partnerships with organizations that share our values, prioritizing open dialogue and a win/win mindset.
Together, we ensure that IT security goals are not only met but exceeded, safeguarding business continuity every day. Our people are our greatest asset, unified by our mission to secure and serve our customers and frustrate the hackers.
Latest Insights & Blog
Expert insights on cybersecurity, compliance, and IT strategy.
-
Payment Remittance Phishing Attacks Security Bulletin
Over the past several days, the TorchLight Security Operations Center has observed a rapid escalation in payment remittance phishing attacks targeting end users across multiple industries. While these phishing techniques aren’t new, the scale and frequency of this week’s activity represent a significant shift in threat actor behavior. In this post, we break down what…
-
What Palo Alto’s Breach Teaches About Protecting SaaS Applications
In August, Palo Alto Networks got breached. Not through their firewall. Not through phishing. Through a Salesforce integration. Over 700 organizations were affected. And their security tools never saw it coming.
-
Strategic Guidance – Getting The Most From Your Pen Test Report
It’s Q4 and pen test reports are piling up. Most companies scan for critical findings, patch them, and move on. But those medium and low-risk findings everyone ignores? They’re revealing where your security posture is quietly deteriorating. Gary Blosser, our vCISO and Principal Security Architect, shows you how to extract real value from every section…
-
Docusign Phishing Attacks Security Bulletin
The TorchLight Security Operations Center has seen a massive increase in fake Docusign phishing emails since Monday of this week. While these threat vectors has been in use since early 2024, the massive rise in attacks this week is real. At this point, consider all Docusign emails to be hostile and must be carefully reviewed…
-
The Palo Alto Paradox: Why Even Security Giants Fall Through Integration Gaps
Recently, Palo Alto Networks fell victim to a cyber-attack. Attackers used compromised OAuth tokens to breach 700+ organizations through a third-party marketing tool integration. If a security giant like Palo Alto can fall through integration cracks, what does that say about your exposure?
-

The Future of Authentication: Why Phishing-Resistant MFA Matters
MFA fatigue is creating security gaps as employees mindlessly click “approve” on authentication prompts. Learn how phishing-resistant MFA eliminates password frustration while stopping credential-based attacks entirely. Augusto Melo explores why this strategic shift cuts breach risk, boosts productivity, and positions organizations ahead of compliance requirements.
-
Why Advanced Cybersecurity Tools Still Fail – And What to Do Instead
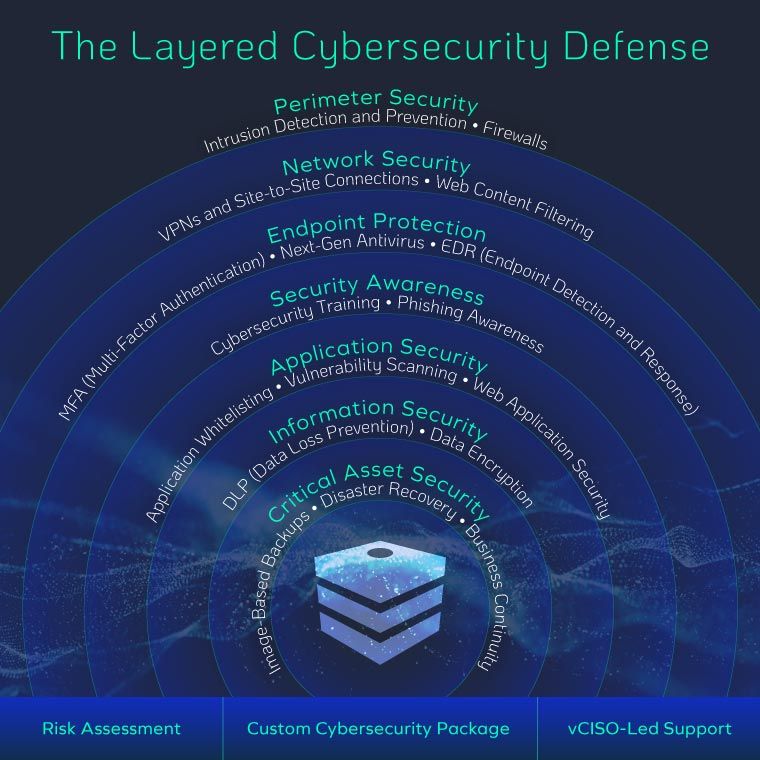
It seems like every week another well-known company falls victim to a cyberattack – even those armed with the latest, most expensive cybersecurity tools. So why do breaches keep happening? After 15 years of breach investigations, one pattern is clear: most organizations lack a holistic approach to security. Tools are important, but without layered defenses…
-
Why We Partnered with Drip7 Security Awareness Training to Tackle the Real Cybersecurity Risk: People
TorchLight has partnered with Drip7 to strengthen human-focused cybersecurity training. Learn how this microlearning platform helps reduce human error, improve security awareness, and support a holistic cybersecurity strategy for your business.
-
20 Ways GenAI Will Reshape Cybersecurity and What It Means for Your Business
Generative AI is reshaping cybersecurity and changing the way businesses operate. In a recent Forbes Technology Council feature, TorchLight CEO Nolan Garrett shared how AI is improving threat detection and response while also introducing new risks, from deepfakes to automated reconnaissance. This post also looks at how AI is transforming industries beyond security, accelerating the…
-
IT Should Be More Than Just Fixing Computers
Learn why SMBs need more than basic IT support – and how a security-first MSP like TorchLight can protect your business from modern cyber threats.
