Microsoft 365 Modern Workplace & Endpoint Security
Reduce complexity. Increase security. Give your team a simpler, safer way to work – anywhere.
TorchLight is your Microsoft 365 security-first partner. We design, migrate, and manage your modern workplace – then support your team every day.
The Modern Office with Microsoft 365
More secure. Less complex. No VPN for everyday work.
Simpler Day-to-Day
Single sign-on (Entra ID) & strong MFA
SharePoint/OneDrive instead of file servers
Teams for chat, meetings & voice
Stronger Security
Defender for Office 365 (anti-phish/spam)
Defender XDR for endpoints
Conditional Access & device compliance
Lower Complexity
Retire file/print servers & everyday VPN
Autopilot deployments & Autopatch
Cloud backup & continuity built-in
| Before (Legacy) | After with TorchLight M365 | |
| Access | VPN, shared drives | SharePoint/OneDrive, zero-trust |
| Devices | Imaging, GPOs | Autopilot + Intune |
| Security | Separate AV/spam/MDM | Defender XDR + Defender for O365 |
| Printing | Print servers | Universal Print |
| Updates | Manual patching | Autopatch + baselines |
Core Capabilities We Implement & Manage
Identity, devices, collaboration, protection, and automation – aligned to your risk profile.
Identity & Access
Entra ID (Azure AD), MFA, Conditional Access, SSO to apps.
Endpoint Management
Intune for Windows, macOS, iOS/Android with Autopilot & compliance.
Collaboration
Teams, SharePoint, OneDrive – reliable, secure collaboration without a VPN.
Protection
Defender XDR for endpoints & Defender for Office 365 for email threats.
Data & Printing
Purview DLP & sensitivity labels; Universal Print (serverless).
Automation
Autopatch, configuration baselines, and lifecycle policy enforcement.
Why TorchLight?
We exist to serve our customers and protect them from relentless cyber threats. We lead with transparency, proactive communication, and a security-first mindset – pairing Microsoft 365 expertise with day-to-day support and measurable outcomes.
Latest Insights & Blog
Expert insights on cybersecurity, compliance, and IT strategy.
-

2026 Cyber Insurance Requirements
Cyber insurance changed. The questionnaire is now an audit, and the controls you check off are the ones you must prove were running when an attacker got in. Here is what shifted in 2026, why claims get denied over MFA, and what it means for credit unions, healthcare, RIAs, mid-market firms, and schools.
-

The LLMShare Attack: When a Trusted AI Link Becomes a Malware Delivery Truck
Attackers have found a way to deliver malware through pages hosted on the real ChatGPT and Claude domains, sailing straight past the security checks that trust those sites. The LLMShare attack is the latest evolution of ClickFix, and it matters whether you already run AI tools or are just deciding to.
-

Support Automation Is Great Until It Becomes an Attacker’s Help Desk: The Meta AI Instagram Exploit and What It Reveals
On June 1, hackers used Meta’s AI support chatbot to take over Instagram accounts belonging to the Obama White House, Sephora, and the Chief Master Sergeant of Space Force. The architecture problem behind it should worry every operator.
-

Why Device Logins Just Became a Liability
A new phishing technique has compromised more than 340 Microsoft 365 organizations since February 2026, and not one of them lost a password. Here is what credit unions, healthcare practices, and RIA firms need to ask their IT team this week, before an examiner does.
-

How Credit Unions Can Stay Audit-Ready Using Outsourced IT Managed Services
How Credit Unions Can Stay Audit-Ready Using Outsourced IT Managed Services Every credit union leader knows the feeling: an NCUA exam is approaching, and the scramble begins, pulling together logs, chasing down documentation, trying to prove that controls are actually in place. It’s stressful, expensive, and entirely avoidable. The root problem is almost always the…
-
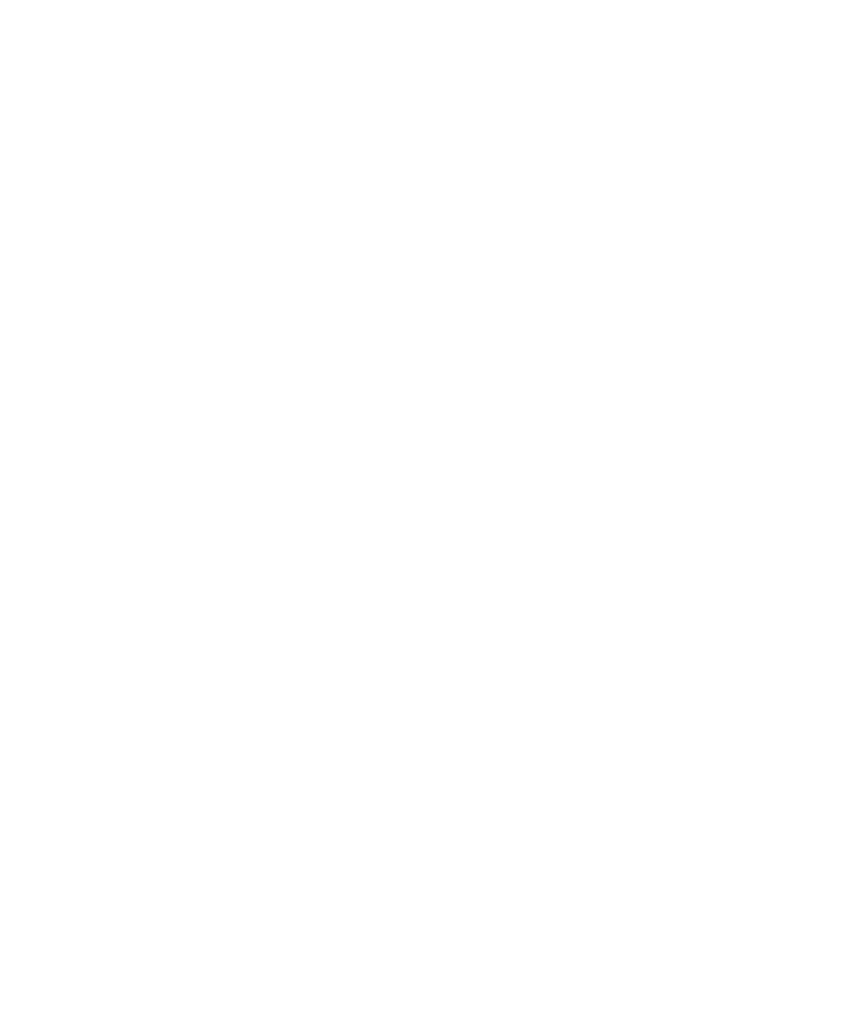
Three Days to Patch a 10.0: What The Cisco SD-WAN Vulnerability Says About Every Network in 2026
Two critical ScreenConnect vulnerabilities, including a CVSS 9.0 flaw under active exploitation by nation-state actors, have opened a direct tunnel into the networks of banks, RIAs, and healthcare practices. The federal patch deadline is May 12, 2026. Here’s what to check, what to hunt for, and how to close the door before examiners or attackers…
-
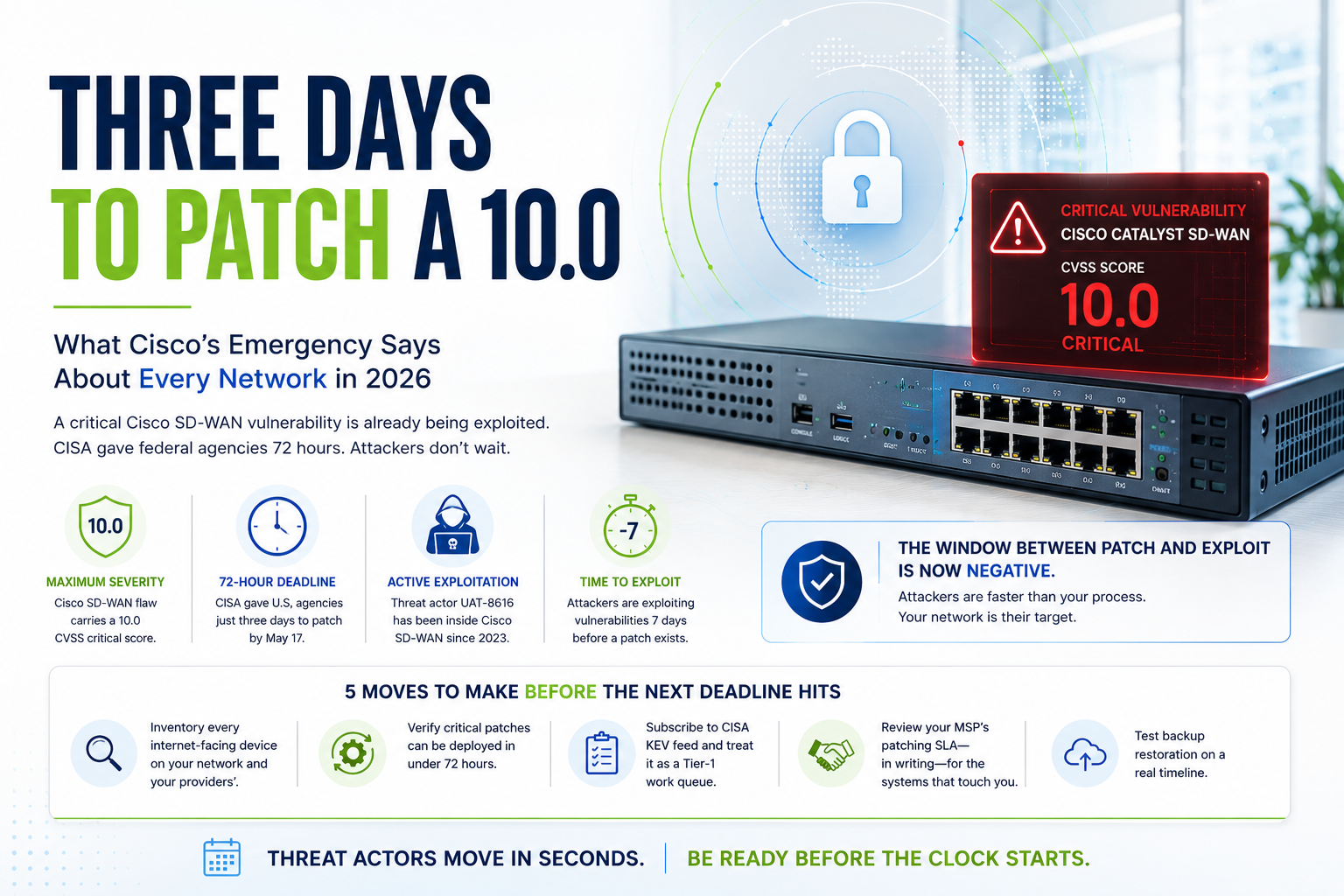
Staff Augmentation vs Managed Services: What IT Leaders Need to Know Before Choosing
Not long ago, the answer to an IT gap was simple: hire a contractor, bring in a temp resource, or extend a vendor engagement. Staff augmentation felt flexible, affordable, and fast. For many organizations, it still has a role to play. But the IT environment has changed dramatically. Ransomware attacks are targeting mid-market companies and…
-

Your Remote Access Tool Could Be Your Biggest Threat
Two critical ScreenConnect vulnerabilities, including a CVSS 9.0 flaw under active exploitation by nation-state actors, have opened a direct tunnel into the networks of banks, RIAs, and healthcare practices. The federal patch deadline is May 12, 2026. Here’s what to check, what to hunt for, and how to close the door before examiners or attackers…
-

Managed IT Services Pricing in 2026: A Complete Guide for Businesses
When businesses start researching managed IT services, one question usually comes first: “How much should managed IT actually cost?” And honestly, the answers online can feel confusing. One provider may quote a few hundred dollars per month, while another charges thousands for seemingly similar services. Some include cybersecurity, backups, and cloud management in their pricing,…
-
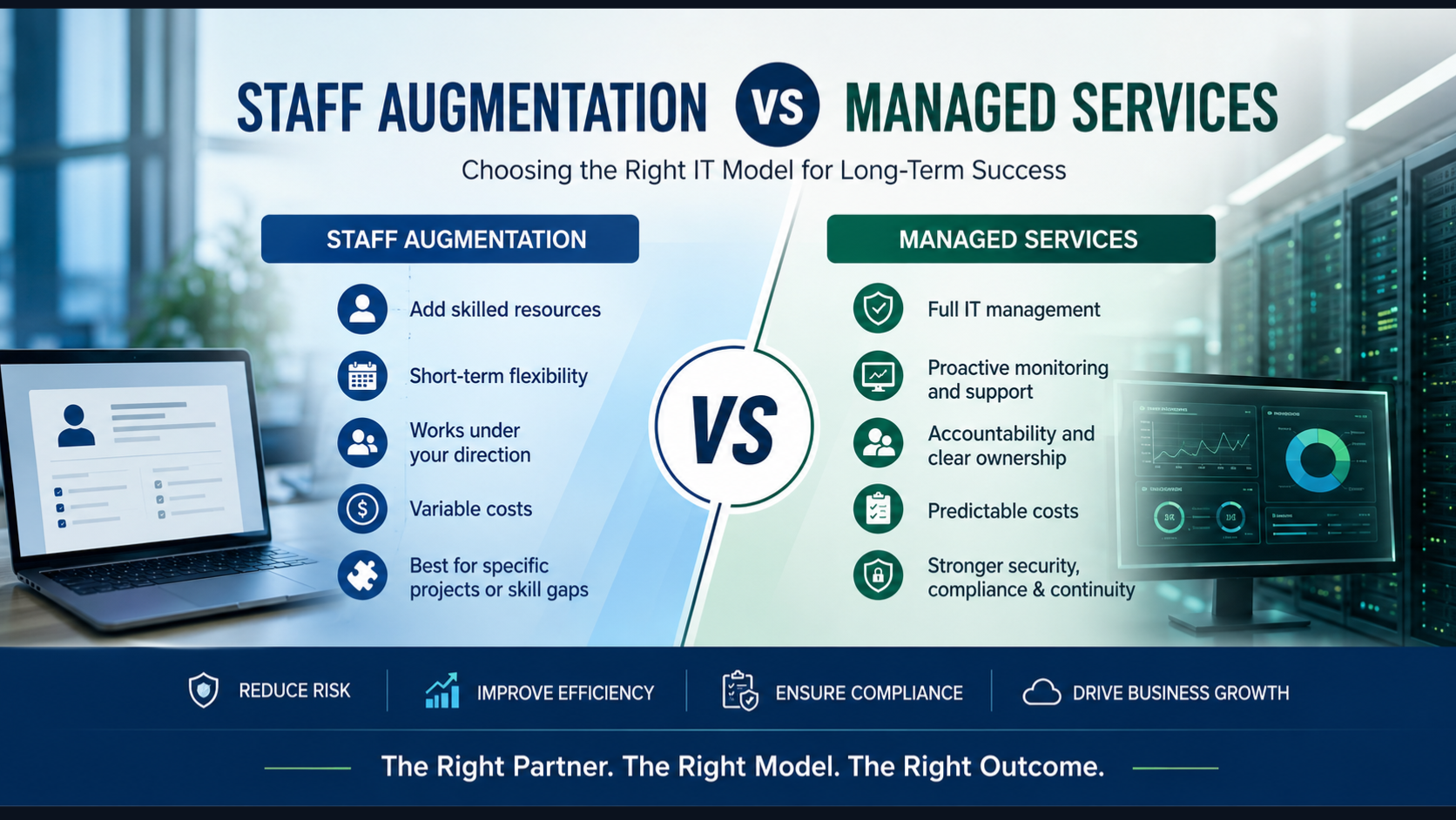
271 Bugs in Firefox! What Mozilla’s AI Disclosure Means for Your Security Team
Surfacing 22 new bugs in Firefox 148 was already an outlier. Surfacing 271 in Firefox 150 was something else entirely.
