Professional IT Services
Design, Build, Migrate, Success
Microsoft Gold Certified Experts in M365 Migration & Support
Microsoft Azure Specialists For Cloud Enablement & Security
Engineering & Implementation Services
Start With An Idea, Create An Outcome That Transforms Your Business
Assessment
We observe and assess current servers and networking transport.
Design
Our Cloud Architects design an architecture that supports the desired outcomes.
Build
TorchLight Cloud Engineers prepare the infrastructure for data and migrate selected data.
Implementation
Testing starts with a selected group and rolls out to all users company wide.
Why TorchLight?
At TorchLight, our “why” is simple: we exist to serve our customers and protect them from the relentless threat of hackers. This mission drives everything we do, setting us apart in the Secured and Managed IT landscape.
We foster a culture of candor, transparency, service, proactive communication and a growth mindset, all aimed at supporting our clients’ needs. We seek trusted partnerships with organizations that share our values, prioritizing open dialogue and a win/win mindset.
Together, we ensure that IT security goals are not only met but exceeded, safeguarding business continuity every day. Our people are our greatest asset, unified by our mission to secure and serve our customers and frustrate the hackers.
Latest Insights & Blog
Expert insights on cybersecurity, compliance, and IT strategy.
-
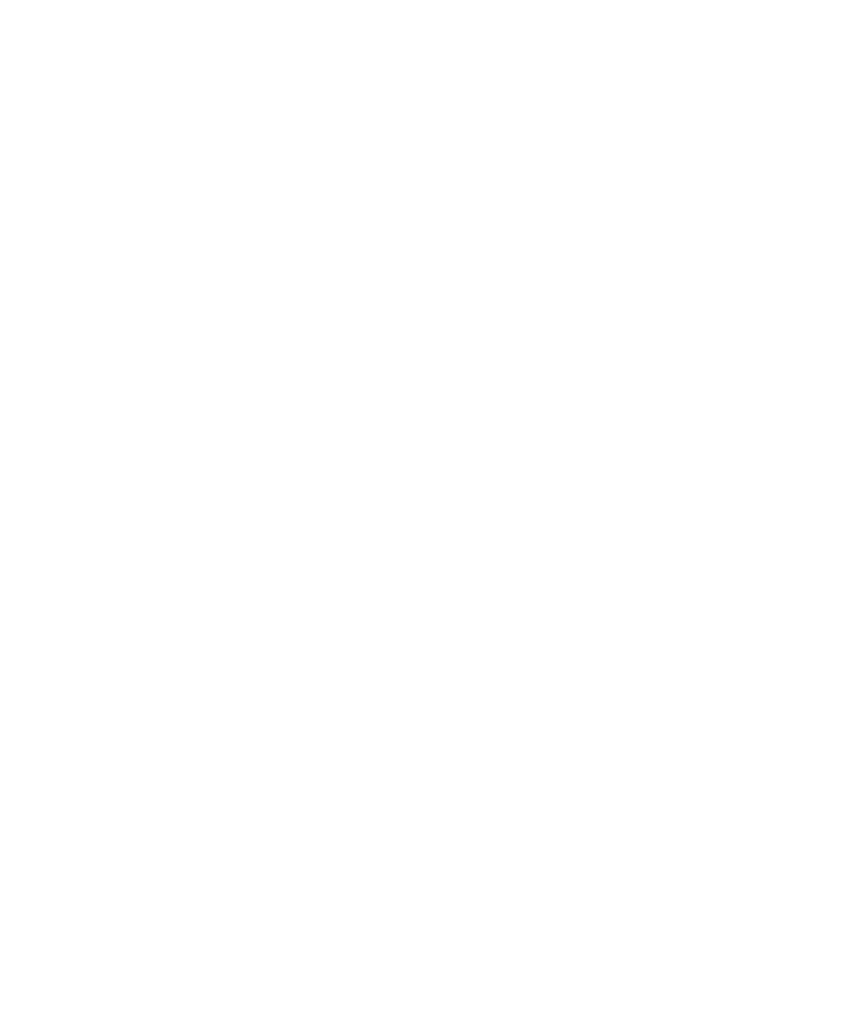
Staff Augmentation vs Managed Services: What IT Leaders Need to Know Before Choosing
Not long ago, the answer to an IT gap was simple: hire a contractor, bring in a temp resource, or extend a vendor engagement. Staff augmentation felt flexible, affordable, and fast. For many organizations, it still has a role to play. But the IT environment has changed dramatically. Ransomware attacks are targeting mid-market companies and…
-

Your Remote Access Tool Could Be Your Biggest Threat
Two critical ScreenConnect vulnerabilities, including a CVSS 9.0 flaw under active exploitation by nation-state actors, have opened a direct tunnel into the networks of banks, RIAs, and healthcare practices. The federal patch deadline is May 12, 2026. Here’s what to check, what to hunt for, and how to close the door before examiners or attackers…
-

Managed IT Services Pricing in 2026: A Complete Guide for Businesses
When businesses start researching managed IT services, one question usually comes first: “How much should managed IT actually cost?” And honestly, the answers online can feel confusing. One provider may quote a few hundred dollars per month, while another charges thousands for seemingly similar services. Some include cybersecurity, backups, and cloud management in their pricing,…
-
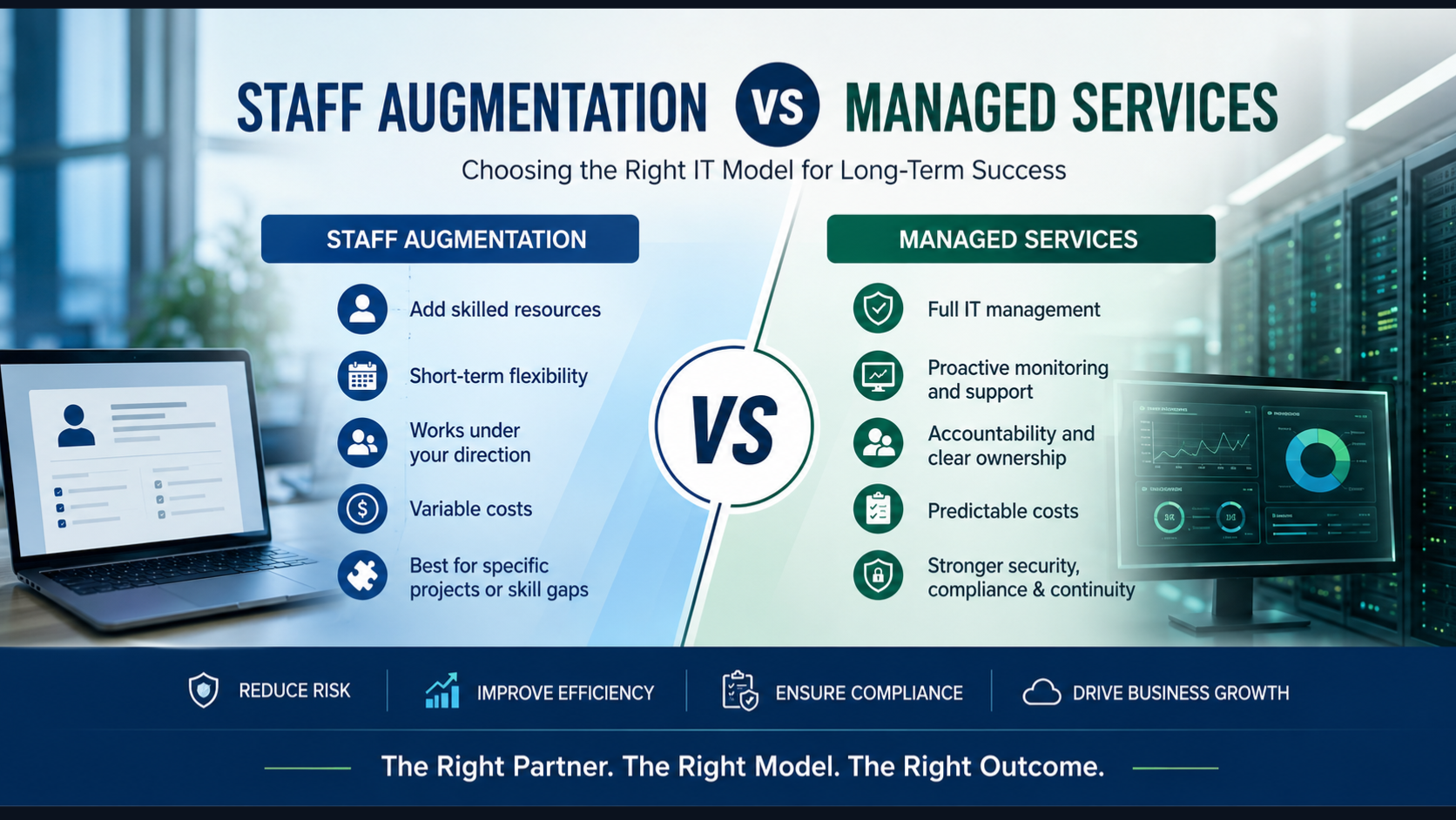
271 Bugs in Firefox! What Mozilla’s AI Disclosure Means for Your Security Team
Surfacing 22 new bugs in Firefox 148 was already an outlier. Surfacing 271 in Firefox 150 was something else entirely.
-

AI Phishing Attacks in 2026: Why Regulated Organizations Are at Risk
Phishing volume and sophistication have surged in 2026, driven by generative AI that lets attackers produce flawless, personalized lures at scale. Traditional email filters and “spot the typo” training can’t keep up.
-

Why Regulated Businesses Need Managed Security Services (MSSP) in 2026?
Executive Summary Managed Security Services Providers (MSSPs) deliver 24/7 threat monitoring, detection, and response capabilities that most organizations can’t build cost-effectively in-house. For regulated industries—credit unions, healthcare providers, government agencies, and wealth management firms—MSSPs have evolved from optional vendors to strategic necessities. This comprehensive guide explains what MSSPs actually do, who needs them, how to…
-
AV vs EDR vs MDR vs ITDR: What Regulated Organizations Actually Need in 2026
The Cybersecurity Tool Problem No One Talks About Here’s a conversation that happens more often than it should in boardrooms across financial services, healthcare, and government sectors: “Do we have antivirus?” the executive asks. “Yes,” the IT manager confirms. “Then we’re protected, right?” “…Sort of.” That “sort of” is where data breaches live. That hesitation…
-

Microsoft Defender vs Traditional Security Tools: What Actually Wins?
Every organization running Microsoft 365 faces the same question eventually: is the security baked into our Microsoft subscription actually protecting us — or are we spending money on tools we’ve already paid for while leaving real gaps open? It’s a fair question. And if you’re in a regulated industry — a credit union, a healthcare…
-
The AI That’s Too Dangerous to Release (And What It Means for Your Business)
A few weeks ago, Anthropic accidentally left nearly 3,000 unpublished internal files exposed on the public internet, no password required. Among those files was a draft blog post describing what the company called “by far the most powerful AI model we’ve ever developed.”
-
Google Proposed Device Bound Session Credentials To Prevent Session Theft – Will This Solve The Problem?
Google just rolled out something called Device Bound Session Credentials — DBSC for those who enjoy acronyms. But like most things that arrive wrapped in a press release, it’s worth taking a closer look before you decide whether to applaud or raise an eyebrow.
